Abstract
1. Introduction
Wireless sensor networks (WSNs) consist of a few base stations (BS) and a large number of low-cost sensor nodes which have constrained communication and computation resources. Each sensor node comprises a sensing unit, a data processing unit, a short range communication module, and a power supply unit [1]. WSNs have a huge potentiality in many application fields such as military target tracking, hazardous environment exploration, and biomedical health monitoring. Due to the limited power supply of the sensor nodes, some researches [2–5] have introduced the mobile sink into the resource-constrained WSNs to prolong the sensor network's lifetime. However, almost all of the existing schemes focus on the mobility strategies of the mobile sink and few studies mentioned the security issues of using mobile sink in the resource-constrained WSNs.
In some scenarios, such as military target tracking and biomedical health monitoring, sensor nodes need to transmit confidential data via the wireless networks. However, due to the wireless nature of the sensor networks, any user (including the malicious users or adversaries) is able to eavesdrop or tamper with any sensitive collected data transmitted in WSNs. Therefore, the authentication between mobile sinks and sensor nodes is necessary and important for sensitive applications in WSNs, which can ensure that the confidential data collected by the sensor nodes are transmitted to the legitimate collectors securely.
To address the above-mentioned issue, in this paper, we propose an authentication scheme that provides authentication and session key agreement between mobile sink and cluster head (CH, a special kind of sensor nodes which play the role of the base station in each local cluster). The proposed authentication scheme can solve the authentication problem and provide data confidentiality when using mobile sink in WSNs. In addition, in the authentication phase of the proposed scheme, the mobile sink and the cluster head can exchange the authentication message to authenticate each other without the participation of the base station, while most of the existing authentication schemes need three communication entities (the user, the sensors, and the base station) to exchange message for verifying each other in WSNs. Therefore, the proposed scheme is more flexible than three-communication-entity based authentication scheme when using mobile sinks in WSNs.
The remainder of this paper is organized as follows. Section 2 reviews existing related works on user authentication in WSNs. In Section 3, the preliminaries, network model, and some assumptions used in this scheme are discussed. The proposed scheme and corresponding protocol analysis are presented in Sections 4 and 5, respectively. Finally, Section 6 concludes the paper.
2. Related Work
In recent years, the security issue in WSNs receives increasing attention due to the inherent open nature of the WSNs. In this section, we briefly describe some mainstream security mechanisms in resource-constrained WSNs.
2.1. Key Establishment Protocols in WSNs
Eschenauer and Gligor [9] proposed a random key predistribution scheme to establish the initial trust among the sensor nodes. In their scheme, a set of keys from a key pool is selected randomly and stored in the sensors before the sensors are deployed. As a result, any two sensor nodes have a certain probability to share at least one common key. Chan et al. [10] extended this idea and proposed two key predistribution schemes: the
2.2. Password-Based Authentication Scheme in WSNs
In 2004, Watro et al. [12] proposed an authentication scheme for WSNs using the RSA protocol and Diffie-Hellman protocol, namely, TinyPK protocol. However, TinyPK protocol is vulnerable to masquerade attack [6]. Then, Das [6] presented a two-factor user authentication protocol for WSNs to remedy this weakness, but Chen and Shih [7] pointed out that Das's scheme fails to achieve mutual authentication. Later, Chen and Shih proposed a novel mutual authentication protocol for WSNs [7]. He et al. [8] proposed an improved authentication scheme based on Das's scheme. Their improved scheme can resist the security weaknesses such as insider attack and impersonation attack. In 2010, Yuan et al. [13] proposed a biometric-based user authentication scheme for WSNs. The architecture of Yuan et al.'s scheme is similar to Das's scheme. However, their scheme still suffers from node compromise attack and denial-of-service attack [14].
In recent years, some researchers have suggested to introduce the mobile sink in WSNs to prolong the lifetime of the resource-constrained WSNs. Most of the existing works focus on data gathering applications and energy consumption [5, 15]. Vupputuri et al. [5] proposed a scheme that uses mobile data collectors to improve the network lifetime of WSNs. In [15], the authors suggested a multisink distributed and localized algorithm for improving sensor network lifetime. The authors of [3] provided a survey on mechanisms that utilize node mobility to prolong the network lifetime and then presented a comparison of these mechanisms.
However, there are few studies focusing on the security problem when using mobile sinks in WSNs. We believe that the security and authentication problem of mobile sink node is very important in WSNs. If there is no relevant security mechanism deployed in WSNs, the data security of WSNs is suffering more challenges. For example, the adversary may impersonate as a legal mobile sink to collect the sensitive sensed data from sensors or impersonate as a legal sensor to upload inaccuracy or false messages to the mobile sink. In addition, owing to the mobility of the mobile sink, the existing related user authentication schemes in WSNs [8, 14, 16] are not suitable for the authentication between the mobile sink and the sensor node. In this paper, we propose a novel scheme using bilinear pairings to enhance data security when introducing mobile sinks into WSNs.
3. Network Model, Assumptions, and Preliminaries
3.1. Network Model
In the proposed scheme, we consider a hierarchical WSN architecture similar to [3, 17]. This is a hierarchy among the nodes according to the function of different nodes: sensor nodes, cluster heads, and base station. The considered network model is presented in Figure 1.

The system architecture of the proposed scheme.
A sensor node is a small device that has limited power, sensing, and computational capabilities, and it is used to collect the environmental parameters in a designated place. Without loss of generality, it is assumed that the sensor nodes are freely distributed. Sensor nodes can communicate with each other in its local cluster and finally deliver the sensed data to a cluster head [1].
Compared with sensor nodes, a cluster head (CH) has more resources in terms of power supply, processing capability, and radio transmission range. Therefore, it can communicate with other CHs directly and transmit the sensed data to the BS directly. The role of the CH is gathering the collected data from its cluster members, saving data in the memory, and then relaying the collected data to an authenticated mobile sink when the mobile sink moves to the vicinity of it.
A base station (BS) is a powerful server with a large range of communication area. The BS is directly linked to the Internet and is used to aggregate data from all the CHs. It is usually regarded as an interface between the WSNs and the Internet. The BS is typically a data collection center or a powerful data processing/storage center. In addition, the BS also serves as the master controller of the WSNs, which controls the activities of the entire network.
The mobile sink is responsible for collecting the sensed data from the CHs and uploading the collected data to the BS. The principal purpose of introducing the mobile sink into the WSNs is to reduce the communication consumption between CH and BS and further prolong the lifetime of the WSNs. In addition, the mobile sink is able to visit all the cluster heads to collect the sensed data in WSNs because of its mobility.
The hierarchical WSNs model has been widely used in many sensing applications because of its superiority on energy saving. For example, in practical applications, the number of deployed sensor nodes is always extremely large and the connectivity between all the sensor nodes is not always necessary. Therefore, the hierarchical WSNs model has more operational advantages than the distributed WSN model for reducing the power consumption of the sensors. Based on these reasons, in this paper, we design the secure authentication scheme for WSNs under the hierarchical WSN architecture.
3.2. Assumptions
In this subsection, we give some basic assumptions for the proposed scheme. As mentioned above, three major system roles (the mobile sink, the CH, and the BS) are used to characterize the system model. Here we introduce the assumptions, respectively.
First, it is assumed that the mobile sink is a handheld terminal with a smart card issued by the BS. The mobile sink is operating correctly only if the user enters the correct user identity and password. Moreover, the mobile sink's storage space is large enough to store the sensed data collected from the CHs. Furthermore, the mobile sink is assumed to be powerful in terms of computing and energy supplies.
Second, since our main goal is to establish the mutual authentication between the mobile sink and the CH, we assume that the secure connections among each sensor in a local cluster have been established using existing secure key establishment schemes [8, 15, 16]. Therefore, we omit the security mechanism that the sensors transmit the sensed data to the cluster head in a cluster.
Third, it is assumed that the BS is protected against various attacks by well-established security mechanisms such as system security and physical security. Furthermore, there are some studies which have been proposed to solve the problem of node capture attack in [18, 19]. Therefore, it is assumed that the BS has the ability to detect the compromised CHs in WSNs. The BS maintains a database table LCD
3.3. Preliminaries
In this subsection, we introduce the concepts of elliptic curve cryptography (ECC) and bilinear pairings. Compared with the RSA algorithm, ECC can achieve the same security level with shorter key length [20].
3.3.1. Elliptic Curve
Let 
3.3.2. Bilinear Pairings
Let
3.3.3. Mathematical Problems
To prove the security of our proposed protocol, we present some important mathematical problems [20, 21] as follows.
To the best of our knowledge, there is no polynomial time algorithm to solve any of the above-mentioned problems with nonnegligible probability [20].
4. The Proposed Scheme
In order to address the authentication problem between the mobile sink and cluster head, we propose a novel authentication scheme using bilinear pairings. The proposed scheme contains five phases, that is, the system initialization phase, the registration phase, the login phase, the authentication phase, the data extraction phase, and the password change phase. For the sake of clarity, the notations used in this paper are listed in the notation section. The detailed descriptions of these phases are in the notation section.
4.1. System Initialization
In this phase, the base station initializes all the needed keys and parameters used in this scheme. The BS performs the following steps.
4.2. Registration Phase
Prior to the system deployment, all the cluster nodes and mobile sinks must be registered to the BS. The registration phase consists of two parts, namely, CH registration and mobile sink registration. In the proposed scheme, each cluster node in the system is assigned a unique identifier

Then, the BS issues a smart card which contains
4.3. Login Phase
When a user wants to use the mobile sink to collect the sensed data in a sensor network, he/she inserts his/her smart card into the terminal and then keys his/her identity

The system architecture of the proposed scheme.

Then, the mobile sink sends the message

Then, the BS checks whether
After finishing the previous steps, the mobile sink contains the latest database table of noncompromised cluster heads. Then, the mobile sink can run the following steps for authentication. Besides, in order to obtain the latest noncompromised cluster heads list, this phase needs to be automatically operated at regular intervals periodically.
4.4. Authentication Phase
After finishing the login phase, the mobile sink can freely move in the cover range of the WSNs to collect the sensed data. The following steps are depicted in Figure 3, and the detailed descriptions are as follows.

The system architecture of the proposed scheme.

Then, the mobile sink sends the message
It is obvious that two session keys are identical by the following equations:

4.5. The Data Extraction Phase
When the mutual authentication is achieved and a session key is established with a CH, the mobile sink can extract sensed data from the CH. The detailed processes are as follows.
The above formula can be deduced as follows:

Then, the BS checks whether
4.6. Password Change Phase
In this phase, the user

Then, the BS sends back the message
5. Security Analysis and Performance Evaluation
5.1. Security Analysis
In this subsection, we evaluate the security of our proposed scheme. Before evaluating the security of our scheme, it is assumed that an adversary may have the following capabilities.
The adversary has the ability to control over the communication channel among the mobile sink, the CH, and the base station. In other words, the attacker may intercept, insert, delete, or modify any exchanged messages in the channel. The adversary may either (i) obtain a user's identity and password or (ii) extract the secret information stored in the smart card but cannot obtain both (i) and (ii). When the adversary steals or obtains a smart card, he/she has no chance to get both the identity and password of the smart card.
As we will see in the following paragraphs, the proposed authentication scheme has been designed to resist against the following attacks.
5.1.1. Replay Attack
A replay attack is an attack where an authentication session is replayed by an attacker to fool a computer into granting access. In order to prevent the replay attack, the timestamp
In addition, when an adversary wants to launch a replay attack to communicate with an authorized mobile sink, he/she needs to send a message
5.1.2. Impersonation Attack
In this type of attack, the adversary forges a valid message
5.1.3. Stolen Smart Card Attack
If the adversary has obtained the smart card of user
5.1.4. Privileged-Insider Attack
During the registration phase of the proposed scheme (in Section 4.2), the owner of the mobile sink
5.1.5. User Anonymity and Untraceability
In the authentication phase of the proposed scheme, the mobile sink sends the message
5.1.6. Resist Node Capture Attack
This resistance is measured by estimating the fraction of total network communications that are compromised by a capture of
In addition, according to the assumption mentioned in Section 3.2, the compromised CHs can be detected by the BS. The BS is able to update the legitimate cluster heads list
When a new CH needs to be added in the existing networks, the BS assigns it a unique identifier
5.1.7. Data Confidentiality
In the proposed scheme, when a mobile sink needs to collect the sensed data from a CH, he/she has to realize the mutual authentication and agree on a shared session key SK with the CH. After establishing the session key SK, the mobile sink is able to receive the encrypted sensed data
After receiving the ciphertext
5.1.8. Proper Mutual Authentication and Session Key Agreement
In the authentication and session key agreement phase of the proposed scheme, the CH can authenticate the mobile sink by checking whether 
On the other hand, the mobile sink is able to authenticate the CH by checking whether
5.2. Performance Analysis
In this section, we first evaluate the performance of our proposed scheme and then compare our proposed scheme with some related schemes. For the convenience of evaluating the computational cost, we define some notations as follows.
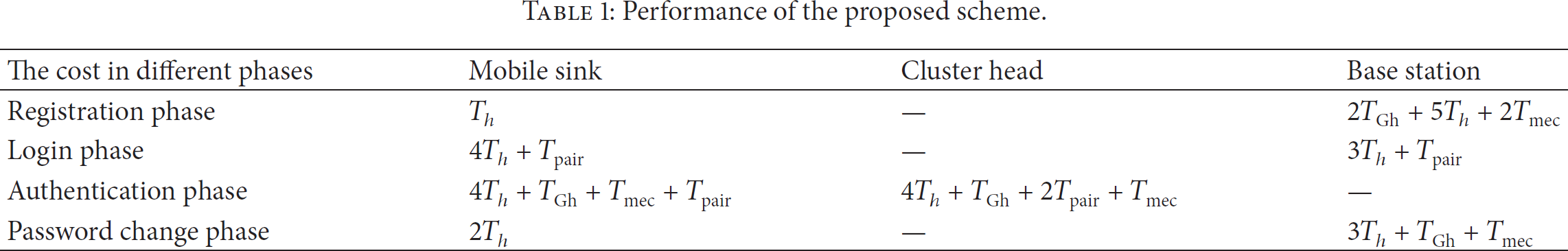
Table 1 illustrates the computational cost of the proposed scheme in different phases. As can be seen from Table 1, our scheme requires
Performance of the proposed scheme.
We implemented a proof-of-concept of our scheme to demonstrate that the proposed scheme is practical enough to be deployed in the resource-constrained WSNs. In our implementation, the mobile sink and the CH operations were developed on an Android smart phone (equipped with a 1.2 GHz ARM processor and 1 GB RAM). The base station operations were developed on an Intel E8400 (3.0 GHz) with 4.0 GB RAM. All the encryption operations are built based on MIRACLE [23]. Table 2 shows the experimental results for related pairing-based operations on the smart phone and the Intel E8400 processor, respectively. According to Table 2, it is obvious that the operation time of bilinear pairings and scalar multiplication is quite short.
Cryptographic operation time.

In Table 3, we demonstrate the execution time of the proposed scheme in different phases. The execution time is measured based on the cryptographic operation time listed in Table 2. From Table 3, we can see that the execution time of the proposed scheme is extremely short. Based on the above analysis, it is obvious that the computational cost of the proposed scheme is well suited for the environment of WSNs.
Execution time of the proposed scheme in different phases.

Communication overhead is closely related to the size of the authentication message. In our scheme, the number of communication parameters includes
The functionality comparison between our scheme and the related authentication schemes is listed in Table 4. Our scheme is secure against replay attack and provides mutual authentication between the mobile sink and the CH. In addition, our scheme prevents smart card breach attack as in Das et al.'s scheme. Based on the above analysis, we can see that our scheme meets the performance requirements and can provide more secure authentication and key agreement function.
Functionality comparison between the proposed scheme and the related schemes.

6. Conclusion
Although there are many studies focusing on the mobile sink, few works focus on the security problem when introducing the mobile sinks in WSNs. In this paper, we have proposed a novel protocol to achieve secure authentication between the mobile sink and the cluster head using bilinear pairings. The proposed scheme can establish a session key between the mobile sink and the cluster head. In addition, after successful authentication, the mobile sink can extract the sensed data from the cluster head using the session key. Security analysis demonstrates that the proposed scheme can solve various security problems when using mobile sinks in WSNs. In addition, the proposed scheme is also efficient in terms of computational. Therefore, our proposed scheme is suitable for the environment of WSNs.
