Abstract
Introduction
Technological advances have been an important factor that increase the productivity and efficiency by determining the direction of industrial development and have led to significant industrial revolutions until today. 1 As of 1765, the first phase of industrialization has begun with the invention of steam engines and steam-powered machines were used in production. In the second stage of industrialization, mass production has started along with the use of production of electricity and the utilization of electricity, oil and chemicals in production processes.2,3
In the third stage of industrialization, electronic and computer systems have been integrated into the industry via programmable logic circuits (PLCs) to automate the production processes. In this phase, the transition from the industrial society to the information society has emerged and the automation of electronics, information and communication has been provided. In this period, technologies such as computer, microelectronics, telecommunication, fiber optics and laser in line with the sciences such as nuclear, biotreatment and biogenetics have shaped the direction of the industrial production.4,5
As of today, with the beginning of the fourth stage of industrialization called “Industry 4.0,” new technologies such as smart robots, health, big data, Internet of Things (IoT), three-dimensional (3D) printers, cloud computing and renewable energy have appeared.6–9 Furthermore, in addition to automation, Industry 4.0 has defined objects that work collaboratively with each other. 10 Likewise, through the sensors of objects, light, image, heat, sound, position, humidity, pressure, proximity, seismic and different types of large volumes of real-world data are collected. Moreover, with the processing of the collected data, real-time communication between objects is ensured and a fast, flexible, human-independent, high-quality and more efficient production process is provided. 11
Cyber-physical systems, the industrial application of IoT, enable the control of a physical environment with cyber infrastructures. 12 The concept of Industrial IoT, which emerged with the creation of cyber-physical systems, has enabled human-free industrial processes by providing machine-to-machine (M2M) communication. 13 Moreover, the machines that communicate in real time via sensors in IoT platforms enable the optimization of industrial production processes using resources efficiently and effectively.14–16
On the IoT platforms, providing cyber security is critical in human-free decision-making processes, independent of human, by means of communication between machines. 17 As a result, given the heterogeneous nature of IoT with different types of objects, its operation in distributed architecture and misuse of objects and constraints (energy, computation, etc.), it is a difficult problem to ensure a high level of security in IoT platforms. 18
With the expansion of IoT, the quality and quantity of cyber-attacks affecting the industry is increasing day by day and the cyber-attacks are directly affecting every aspect of the industry. Significant violations by sector on IoT platforms are summarized as follows:
On the other hand, important challenges in ensuring the safety of IoT are given as follows:
Increasing number and variety of intelligent objects in IoT platforms;
Lack of security policies and procedures to manage security on IoT platforms;
Managing security patches for critical software on IoT platforms;
Increased diversity and number of attacks on IoT platforms.
In this study, we describe IoT-specific vulnerabilities and their features by investigating related security weaknesses and threats. Rest of this paper has been organized as follows. Section “IoT” provides detailed information about IoT. In section “Threats and vulnerabilities,” threats and vulnerabilities of IoT are detailed. In section “A risk-based layered approach to IoT security assessment,” a risk-based IoT security model is presented. In section “Conclusion,” the conclusion of the study is given.
IoT
IoT is a large network of interconnected objects over the Internet, which has been rapidly evolving in recent years. 19 The concept of IoT was first used by Kevin Ashton in 1999. It should be mentioned that Ashton has used this concept while describing the benefits of the Internet-based information service architecture that uses radio-frequency identification (RFID) technology in the supply chain of Procter & Gamble (P&G).20,21
Today, the IoT is seen as a new-generation network that has advanced enough to establish the connection between the real world and the virtual world. Figure 1 visualizes the use of many IoT applications for the use of people, vehicles, houses, cities, trade and industry. As is seen, computers, smartphones, smart sockets, school services, smart grids, smart health, smart office and wearable materials are some of the IoT applications.

IoT applications.
The common feature of IoT applications is that the data collected from intelligent objects with embedded sensors are gathered and used over the network. IoT applications are increasing day by day, expanding the usage areas and making human life easier (Figure 2). In fact, a huge amount of personalized data collected by convenient IoT applications covering smart cities, smart environments, smart metering, security and emergency, retail sales, logistics, smart farming, smart livestock and smart health are being shared and analyzed. 22

IoT growth chart by years.
According to Cisco’s research shown in Figure 3, approximately 50 billion devices are expected to be connected to the Internet as of 2020. 23 Considering that the United Nations’ world population is estimated to be 7.7 billion 24 in 2020, it is estimated that each person on earth will have approximately six electronic devices. In addition, it is estimated that in 2020 smart devices will be brought into daily life because of their communication ability with each other and their environment. At this point, it is being forecasted that the tendency to personalize with IoT platforms will peak and the world will experience a constant change after this stage.

IoT platform.
The personalization trend created using the collected data as a result of the widespread use of IoT platforms has an important place. Data collected through IoT applications can be shared outside of applications, for different purposes such as advertising, marketing, statistics and commercial, without the permit of users.
As a result, these incidents in IoT make it necessary to take new measures by increasing security concerns. 25 Regarding the features of IoT, such as having inherently composed of diverse types of devices, generating big data, serving M2M interaction and providing limited computational and operational power constitute challenges against solutions of the security problems. 26
IoT includes not only collection and employment of data, but also covers inferring enabled intelligent systems that can decide and apply via large data analysis methods by utilizing human-independent M2M interaction when required. 27 Nonetheless, IoT-specific behaviors such as the increasing personalization of IoT platforms and the exclusion of M2M interaction from human control bring increasing demands on security protection.28,29 Misuse of sensors or devices that can communicate directly with each other through M2M interaction without human intervention, the shortcomings of conventional security methods to meet IoT security requirements and the fact that IoT devices can be ubiquitously found anywhere without space limit have made the issue an NP-hard problem. The IoT platform is presented in Figure 3.
The IoT consists of three basic layers, as shown in Figure 4, including the perception layer, the network layer and the application layer. 30 On the other hand, the architecture shown in Figure 5 is a general reference model that can be applied to different application platforms including all components involved in data collection, sharing and processing. 31

IoT reference model.

IoT protocols.
An overview of architecture and protocols
The architecture shown in Figure 4 is a general reference model that can be applied to different IoT application platforms including all components involved in the process of data collection, sharing and processing. 31
The reference model is described below in terms of the layers it is composed of which are given as follows:
The IoT protocols according to the layers are shown in Figure 5 and summarized in the following items:
Moreover, IoT application layer protocols use HTTP to provide web service to end users in application layers. However, since the IoT platform has HTTP high computational complexity, low data rate and high energy consumption, it is not preferred to use HTTP as it is. Therefore, IoT-specific web-based light protocols such as IETF (Internet Engineering Task Force), CoAP (Constrained Application Protocol), Embedded Binary HTTP (EBHTTP) and Lean Transfer Protocol (LTP) are used. 36 The CoAP is an important IoT-specific web protocol that has been developed to be used on restricted nodes and constrained networks (low power, low loss). 37 EBHTTP is a binary-formatted, field-efficient, stateless derivative of the standard HTTP/1.1 protocol. 38 Besides, EBHTTP has been primarily designed to transport small data between resource-restricted nodes. On the other hand, LTP is a lightweight web service migration protocol that enables transparent exchange of web service messages between any resource-restricted devices and server or personal computer systems. 39
Security in IoT
Transport Layer Security (TLS) and its predecessor Secure Socket Layer (SSL) protocols are used to securely communicate by encrypting IoT data transmitted over problematic computer networks having no resource and energy shortages. 40 Meanwhile, in protocols that provide security on the transport layer, authentication is handled via symmetric key distributed by asymmetric encryption with X.509 certificates. DTLS (Datagram Transport Layer Security) protocol has been developed to provide three main principles of security, such as UDP-based integrity, authentication and privacy, to enable the TLS protocol to work more efficiently in slow and problematic networks such as IoT. 41
The location of the DTLS protocol in the IoT architecture is shown in Figure 6. As shown in Figure 6, the DTLS protocol running between the application and the network layer is an important protocol that provides end-to-end transfer security. It should be noted that, in the absence of end-to-end protection, it will be possible to gain unauthorized access and misuse of data through an object seized by the attacker.

Position of DTLS in protocol stack.
The ability of the DTLS protocol to operate in limited environments also prevents the performance-related problems in IoT environments. DTLS consists of two layers: registration protocol and handshake. The data are shared with the client and server using the handshake protocol, while the data are encrypted with symmetric encryption keys with the registration protocol. The process of mutual authentication between the parties that will communicate with each other is handled via the exchange of the encryption algorithm and keys. 42 In Figure 7, the process of DTLS handshaking is presented.

The process of DTLS handshaking.
The registration protocol protects application data using keys created during handshake. 43 DTLS partitions, compresses and encrypts each outgoing message in order to generate the message verification code. Similarly, for the incoming messages, it combines, decompresses and decrypts in order to verify the message.
Another important security element in ensuring IoT security is the access control. Access control mechanisms should be used to manage permissions on the use of network resources of data owners and data sharing agents on a large IoT network.
Threats and vulnerabilities
IoT data collected by connecting heterogeneous objects with different communication features in wired and wireless environments are generally processed via transferring to the cloud computing environment. Thus, in order to ensure the high level of information security in the process from the collection of IoT data to processing, it is necessary to take precautions by knowing the threats and weaknesses in IoT environments.
As is known, IoT is a large platform that involves intelligent objects, sensors, software interfaces and mobile applications. Nevertheless, communication and data processing infrastructures on IoT platforms bring security vulnerabilities and threats while accelerating business processes. Unlike traditional security approaches, new security solutions that take into account IoT constraints and architecture should be created in order to prevent any security breaches that could affect the entire IoT platform. An end-to-end security architecture should be designed and implemented in the IoT, which has a large number of attack interfaces, taking all of the IoT security requirements related to physical environments, objects, sensors and communications into account.17,44
Attacks on IoT platforms are classified as physical, network, data processing and application attacks and instances of IoT attacks according to the layers are given as follows:
Physical layer attacks—jamming, denial-of-service and tampering;
Network layer attacks—man-in-the-middle (MITM), exhaustion, collision and spoofing;
Data processing layer attacks—malware, collision and unfairness attacks;
Application layer attacks—Trojans, viruses, malicious code injection and social engineering–based attacks.
As shown in Figure 8, internal and external attacks threaten the layers of IoT such as physical, network, data and application. The details of the suggested layered threat approach presented in Figure 8 are described in the following subsections.
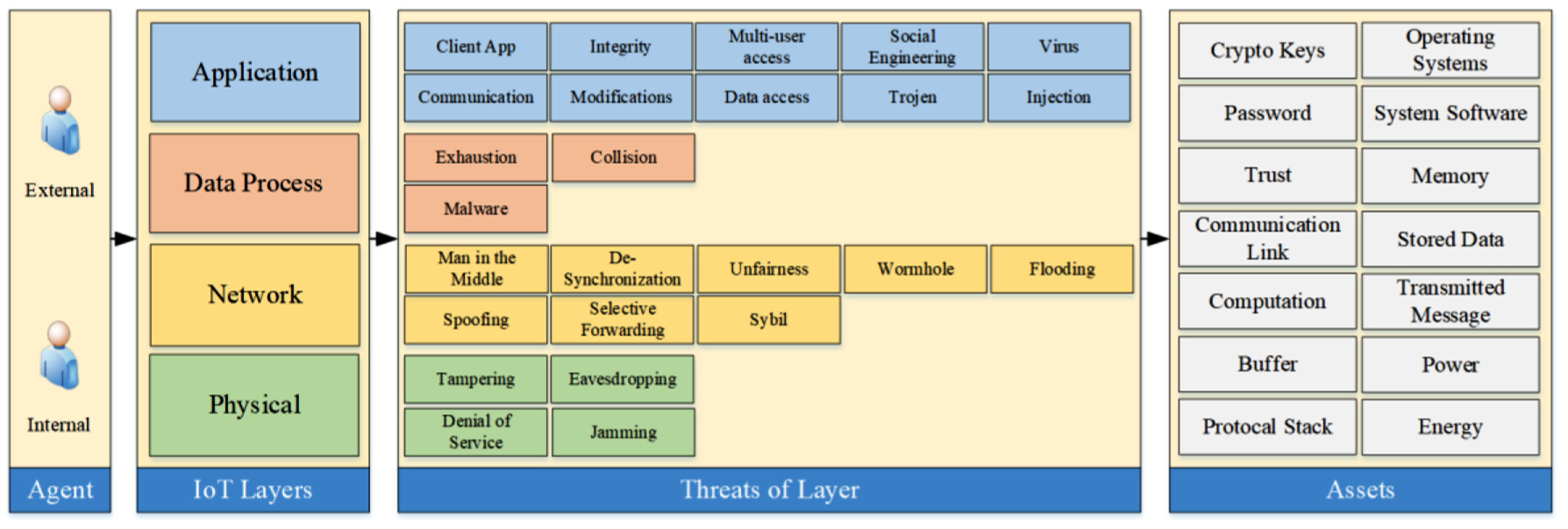
Threat classification according to IoT layers.
Location of attack
Attacks on IoT platforms are carried out in two different locations such as internal and external. The internal attacks made by the users or objects classified as “trusted” due to having access privileges within the platform significantly affect all the layers of IoT. Similar to the internal ones, external attacks by users or objects that exist outside the platform and having no special access privileges also affect all layers of IoT platforms. Nonetheless, the impact of internal attacks on IoT may be more severe since the internal attacks are less controlled than attacks from outside the network. While external attacks can be prevented by network firewall, intrusion detection and attack prevention systems, internal attacks can reach their goal without going through any security tool or mechanism. Thus, attacks within the network are more likely to be successful.
Physical layer
The physical layer of IoT platforms is the layer where objects, sensors and actuators take place in data generation. Moreover, the physical layer of IoT is targeted by attacks such as tampering, eavesdropping, denial of service (DoS) and jamming. Besides, the most vulnerable interface of IoT platforms is the sensors since they can easily be exploited as they are the devices which collect data directly. Yet, in most of the cases, sensors are directly targeted by attacks of tampering and jamming.
Tampering
In the type of attacks which are called tampering, the hardware or software features of IoT objects are modified by the attackers via physical or cyber methods. Furthermore, with the attacks of tampering targeting the physical layer, attackers can violate fundamental security policies such as privacy, availability and integrity by providing direct access to all IoT objects. 45 Tampering targets the integrity of IoT systems.
Jamming
By definition, jamming is the type of attack in which the data integrity is damaged by interfering the network traffic during the communication of the sender and receiver objects. In jamming attacks, positioned between the sender and the receiver, the jammer transmits a high-power signal across the sensitive band range in order to disrupt the communication medium between the objects and violate fundamental security principles such as integrity and accessibility. Jamming is one of the most dangerous types of attacks used to block the IoT network and data exchange between IoT objects communicating wirelessly. This situation is visualized in Figure 9. The “hs” signal sent to the IoT objects by the source is also received by the reactive jammer. Nevertheless, the jammer disturbs traffic by emitting the “hj” signal and suppressing the receiver sensors of the IoT objects.46,47 Jamming targets the accessibility of IoT systems.

Jamming attack.
Eavesdropping
Eavesdropping is a technique that is used to access and retrieve the communication traffic between IoT objects. Encryption methods are applied in order to eliminate the threat that occurs as a result of eavesdropping. Meanwhile, IoT sensors are generally simply designed and low-energy-consuming end devices. Due to the limited functionality of the IoT sensors, security measures such as encryption are made on the hardware. It should be noted that, in eavesdropping, a passive listening attack is made when the communication packet is not changed and the sender does not get any feedback. This method has been named as “replay attack.”48,49 Eavesdropping targets the confidentiality of IoT systems.
DoS
DoS attacks are being made to disrupt the services of IoT platforms. In detail, the communication network between IoT objects is blocked resulting in being non-communicating. The use of IoT in many areas, heterogeneous structure, resource constraints and the multitude of objects in the network make it difficult to get protected from DoS attacks. The security of IoT objects’ communication can be ensured by end-to-end or point-to-point encryption techniques. 50 However, IoT has a weakness against attacks that disrupt its functioning, occupy resources and consume the energy of devices. The most important type of attack affected by such weaknesses is the DoS attacks. Likewise, DoS attacks can target all of the physical, data link, network, transmission and application layers of TCP/IP. Moreover, any weakness in TCP/IP—the main Internet Protocol (IP)—also threatens IoT. As shown in Figure 10, the attacker gets control of the target system by sending a continuous data request to the target IoT platform from different locations using the computers he has converted to “zombie.”51,52 DoS targets the accessibility of IoT systems.
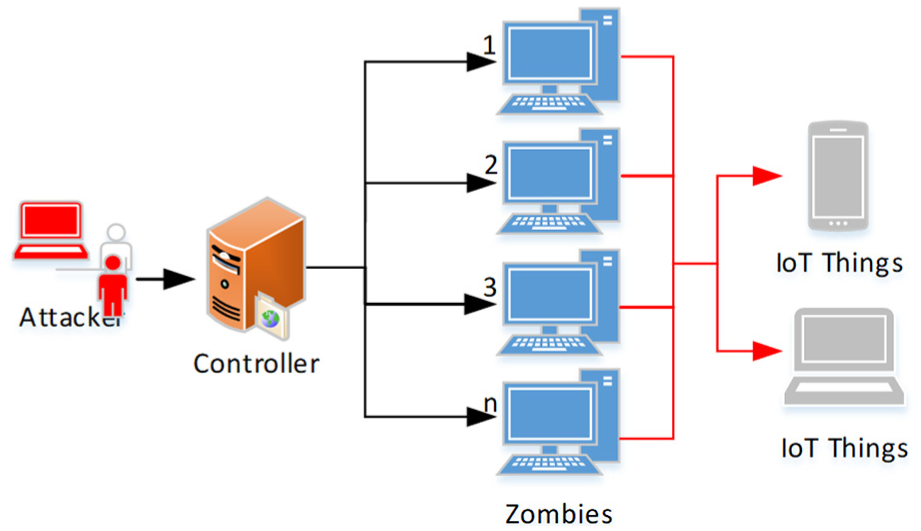
Denial of service attack.
Network layer
Network attacks on IoT platforms, where real-time data collection and data processing are carried out, have very serious consequences. The network layer on the IoT platform is the target of various cyber-attacks such as in information systems. Some of the IoT attacks were listed and explained below.
MITM
The MITM attack is a type of attack to capture, read and modify data between two communicating objects on the IoT platform. 53 Data packets that do not communicate between objects in the network can be captured by all objects connected to the same network. Furthermore, network objects can intervene and read the contents if desired. Thus, the goal of the MITM attacks is to change the data content by capturing and replacing the data packets on the IoT platform via sabotaging the traffic. What is worse is that IoT can have a lot of neglected, open and uncontrolled objects. These objects, for which security has been compromised in IoT networks, have the potential to be the source of MITM attack traffic. Figure 11 shows the MITM attack process.53,54

MITM attack.
Note that the complete elimination of MITM attacks is very challenging and can only be reduced with a good security policy. IoT devices are manufactured for specific purposes and therefore their safety can also be provided according to certain policies. In addition, however, the number and diversity of IoT objects make it difficult to provide the IoT security. This situation causes security weaknesses in the IoT and MITM attacks start threatening IoT.55,56
Spoofing
Data on IoT platforms are usually encrypted through the network traffic and data packets carried via the routing protocol are transmitted by the IP address. Attackers can emulate, modify or resend IP addresses or transport protocol information (UDP, TCP ports, etc.) to poison network traffic. In order to create spoofing attacks, it is possible to generate routing nodes, extended or shortened transmission paths and false error messages.25,52 Figure 12 shows a spoofing attack. Spoofing targets the integrity of IoT systems.

Flowchart of an example spoofing attack.
Desynchronization
The desynchronization attack is a wireless communication attack. On IoT platforms, objects mostly communicate using wireless communication. The way the attackers apply is to make the communication desynchronized via interfering with the communication parameters of the objects which initially communicate synchronously. As a result, desynchronizing the traffic of the objects communicating synchronously causes network traffic not to work properly.57,58
Selective forwarding
The IoT consists of intelligent and multiple objects that require multiple routing for communication between objects. Moreover, in IoT networks, a node seized by an attacker can change network traffic by reducing some data packets and redirecting to different locations. Thus, the data that should reach its target may be missing or corrupted. 59
Unfairness
Unfairness is a repeated collision attack that can also be referred to as exhaustion-based attacks. Data link layer–based attacks usually aim to disrupt the equal load sharing mechanisms of wireless sensor networks (WSNs). This method of attack may cause takedown of a service, and if the number of nodes increases, the impact of the attack gets spread. 60
Wormhole
By definition, a wormhole is a maliciously crafted and low-latency link where the attacker can replicate messages. In a wormhole attack, the attacker sends packets at a point in the network to another point on the network through the tunnel and then sends them back to the network from there. 18
Sybil
Sybil attacks are performed using network objects or devices with multiple IDs in order to generate multi-source and distributed network traffic. Furthermore, Sybil attacks sabotage equal resource usage of IoT platforms. Although malicious nodes are fake, they act as real nodes, producing extra and unnecessary network traffic. In this way, resource consumption of the network increases and causes the network with limited resources to be halted. Sybil attackers manipulate fake abuse pseudo-identities to compromise the effectiveness of the IoT. 61
Flooding
Flooding attacks are one of the most common types of attacks to disable all or part of the IoT network. Flooding attacks can reduce the speed of traffic flowing between objects on the IoT platform and are capable of stopping the network via occupying the hub or node’s resources. In flooding attacks, network traffic is reduced or stopped completely by occupying Domain Name System (DNS) connections of IoT objects. 62 Figure 13 shows a flooding attack. Flooding targets the accessibility of systems.

A schematic illustration of a flooding attack.
DNS flooding attacks directly affect DNS servers using high bandwidth connections of IoT devices. The volume of requests from IoT devices disrupts the services of the DNS service provider and prevents real users from accessing their DNS servers. 63
Data processing layer
The data collected using sensors in IoT are generally processed in cloud systems and this process generates the data processing layer. Attacks on the data processing layer are performed using malware that is embedded in data from edge nodes or sensors.
Exhaustion
Exhaustion attacks aim to interrupt the data processing of the IoT infrastructure. There is no high risk for this kind of attacks since these attacks occur in a higher layer and the ecosystem of the IoT is distributed. It should also be noted that, in cloud-based systems, it is much easier to implement protective measures against the exhaustion attacks. 25
Malware
It is the general name of malware that threatens IoT infrastructures such as viruses and Trojan horses. Malware can penetrate information systems as a plug-in of software, or it can infiltrate computers from the website. Malware is a malicious software which is injected into the data of IoT platforms in order to grant access for seized cloud or distributed systems. Furthermore, malware-based attacks are difficult to detect and prevent. Therefore, it is not enough to have a strong firewall, rather it is also necessary to take protective measures before the data processing stage. 64
Collision
Collision is a jam-type attack since it targets the data transfer and data link layers on IoT. Even if the data traffic is not completely stopped in such attacks, it may be intended to make the network unusable. 18
Application layer
The application layer is the layer where end users communicate with the IoT platform directly. Application layer is employed for several tasks including report generation, querying, analysis and visualization of the data, authentication and interaction with IoT. On IoT platforms, methods such as authentication and restriction of data access can be used to provide security to the application layer. A large amount of data are continuously generated in IoT environments, which also makes it difficult to store such amounts of data. Therefore, it is also difficult to secure the application layer.
Client application
The application layer is the layer where people or machines communicate directly with IoT platforms. At this point, the human–machine interface (HMI) is used for this communication. The HMI facilitates the use of IoT platforms in the application layer while also constituting weaknesses against cyber-attacks. It should be noted that the most common threats in this field are related to the vulnerabilities of web environments. Likewise, in order to access IoT system configurations, devices use the HTTP, which is also important in web application security. In fact, malicious software can infiltrate the IoT system via client-side vulnerabilities. Such attacks, instead of directly damaging the system, remain in the passive mode and cause faulty production on the outputs of the system. In order to filter out such applications in IoT, malware detection and antivirus solutions should be used. In addition, the IoT client application status, operating system status or hardware status should not depend on the state of the other parts of the IoT system. The status (e.g. active, sleep, failure) should not have any negative impact on the layers such as data processing, network or physical.65,66
Communication
In order to weaken the IoT platforms, it is necessary to be able to enter the configuration interface or the communication channel. Applications allowing remote configuration of the IoT system, including the physical layer, provide remote access to systems that they normally configure.
System integrity
System integrity is an important feature of IoT systems and the disruption of the integrity on IoT platforms leads to security risks and threats. The system must continue to operate during high workload or abnormal work processes without compromising system integrity. Besides, in order to test the integrity of the IoT platform, a complex and reliable stress test should be performed.
Modifications
It is also possible to observe security weaknesses due to changes in IoT platforms, such as environmental, systemic and configuration changes. As IoT platforms grow, weaknesses due to system changes may lead to greater problems and impacts. The security vulnerabilities caused by the changes can be minimized by thorough verification of system elements, complex tests and continuous system monitoring.
Multi-user access
IoT platforms must have multi-user access and adequate security level. Furthermore, when the configurations of the IoT system partitions are changed by users, the simultaneous modification of the configuration files and the simultaneous operation of configuration changes can cause conflicts of updates. As a result, a careful process should be planned for multi-user systems.
Data access
Data access security measures should be seriously considered in the application layer. Data access security measures should be rearranged in case of system status change with the update and configuration change made on IoT platforms.
Social engineering
Social engineering, in essence, is the act of capturing and manipulating people’s confidential information. The kinds of information that the attacker wants to gather vary according to purpose, and they can often apply deception methods to collect people’s passwords or confidential information such as banking information. Social engineering attacks can be done via e-mail/website or by one-on-one interview with the victim.
The threat area of social engineering is expanding since the IoT environments involve social engineering tools such as industrial control systems and smart industrial objects. Thus, it can be deduced that the impacts of social engineering go beyond the cyber environment and eventually physical damages come true. Some of these impacts were listed as follows:
Deactivation and damage to production facilities;
Death and injury due to deterioration of signaling of transportation systems such as trains and trams;
Damage to water treatment plants;
Damage to nuclear power plants.
Cyber events in cyber environments such as computers will now be seen in physical environments such as an automobile’s control panel, intelligent heating systems or medical systems. Attackers do not need to have direct access to attack physical cyber systems, rather they can access the distributed structures of the system instead of direct access and manipulate the entire industrial infrastructure. This manipulation is achieved by seizing the sensor nodes, where the objects are connected to each other via the broadband router in an unencrypted fashion. Figure 14 shows a manipulation on a smart IoT system using the deception method.
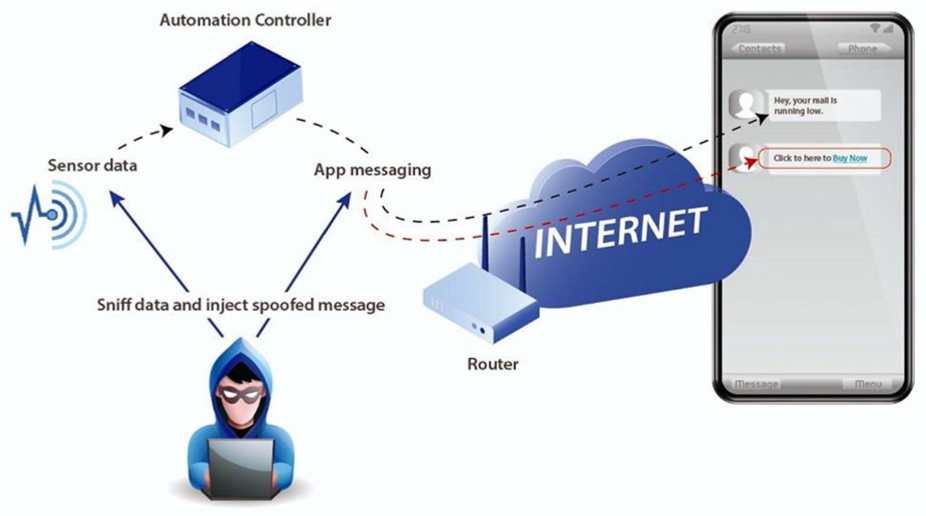
Flowchart of a fake message–based attack to a smart IoT system.
It is a well-known fact that social engineering attacks and exploitation against IoT’s smart objects are observed. For instance, from December 2013 to January 2014, 100,000 e-mails per day were identified as IoT targeting cyber-attacks which aim at firms and individuals. Furthermore, in industrial environments, IoT botnets carry out cyber-attack using a network connection to all intelligent objects.66,67
A risk-based layered approach to IoT security assessment
On IoT platforms, it is essential to ensure high level of security in order to stay secured against various unwanted cases such as unauthorized usage, modification and disclosure of data. Moreover, security vulnerabilities occur when IoT platforms fail to provide any of the three fundamental security elements known as “privacy,”“integrity” and “accessibility.” In order to ensure a high level of security of IoT platforms consisting of sensors and intelligent objects, a new approach with four layers has been proposed to determine the threats and weaknesses according to the layers and to take countermeasures based on three fundamental elements of security according to the risk-based assessments. With the layered IoT security approach, it is aimed to minimize or prevent the impact of security attacks via risk assessments.
The risk-based layered security approach is based on the following four stages:
Securing the layers;
Understanding and evaluating layered threats;
Measuring the likelihood of layered threats;
Determination of layered risk by combining the probability and impact of the layered threat.
Following the risk assessment, a high level of protection is ensured by taking security measures in accordance with its own risk level on each layer.
Securing the layers
The four-tier IoT architecture based on the risk-based layered IoT security approach is shown in Figure 15.

Layered IoT architecture.
Understanding and evaluating layered threats
In order to evaluate the impacts of possible threats on IoT platforms, the impact levels given in Table 1 have been defined.
Level of impacts and their descriptions.

IoT: Internet of Things.
Impact assessment is performed on nodes in IoT platforms. The questions and evaluations given in Table 2 have been used to obtain the security parameters in terms of confidentially, integrity and accessibility by taking into account the elements such as the number of threats to each node, layers affected by the threats on the node, size of the attack surface and the criticality of the node. Among the impact assessments obtained as shown in Table 2, the highest impact value indicates the measurement result of the threat level according to the suggested risk-based layered approach.
CIA risk assessment table.

CIA: confidentiality, integrity and accessibility.
Measuring the occurrence likelihood of layered threats
In this section, it is aimed to understand the general threats to IoT security and to evaluate the likelihood of these threats. In order to facilitate this process, assessment questions regarding threats on IoT platforms have been defined. The evaluation questions are discussed in four main headings (Table 3) as follows:
(a) Measuring threats to the layers;
(b) Processes/procedures for data security in the layers;
(c) Third parties and human factors affecting the security of the layers;
(d) Criticality of the layers and the scale of the attack surface.
Measuring the occurrence likelihood of layered threats.

XSS: cross-site scripting; IoT: Internet of Things.
The probability of occurrence of each threat for layer evaluation fields is defined (Tables 4 and 5) as follows:
Low—the lowest probability of the threat to occur.
Medium—although it is low, there is a likelihood of the threat to occur;
High—it is more likely to have the threat occurrence.
Rating of probability of assessment fields.

Evaluation of threat occurrence.

Upon evaluating the impact of the likelihood of layer threats, the assessment of security risks on IoT platforms is performed in accordance with Table 6.
Risk assessment.

Green color indicates low risk; yellow color indicates medium risk; red color indicates high risk.
Conclusion
IoT is the infrastructure of different intelligent objects that work with an end-to-end integration with a combination of different systems. A single security solution is not enough to ensure the security of the integrated structure of such a diverse system.
IoT is the technology that enables production systems to enter the new process and launch industry 4.0. IoT-based intelligent production mechanisms consist of self-optimizing and organizing production systems in terms of resource availability and consumption. These systems are possible with the use of new smart services, including product optimization, based on product, production, employee and customer use.
IoT systems carry risks in terms of security and privacy. Without eliminating these risks, the IoT requirements are not adequately fulfilled. Because cyber-attacks on cyber physical systems may threaten human life by causing physical damage to the IoT. IoT has a heterogeneous structure and a holistic cyber security framework should be established to ensure the security of the IoT by isolating heterogeneous systems and defining platform boundaries. Since existing security solutions cannot respond to real-time IoT security requirements and cannot be scaled to cyber-physical systems, they are insufficient to ensure the security of IoT with a heterogeneous structure.
In this study, the application fields of IoT, increasing usage rate by years, architecture and protocols and security requirements are mentioned in detail. Assets that create vulnerability are described by classifying the types of attacks that threaten the physical layer, network layer, data processing layer and application layer of IoT. The contribution of this study is to explain the layers of cyber-physical systems that make up the IoT which were evaluated separately and their vulnerabilities and threats were examined and a security model was proposed. The proposed IoT security model is a holistic security model that evaluates each layer of cyber-physical systems separately against vulnerabilities and threats, based on the risk-level approach to ensure IoT security.

