Abstract
Keywords
Introduction
Internet of things (IoT) or the Internet of everything (IoE) is the realization of a panoply of smart and networked devices that serve human needs such as food, clothing, accommodation, transportation, and entertainment.1,2 Future consumers will be able to use smartphones to lock or unlock their homes, to switch lights on or off, to monitor energy consumption, to monitor security, and to control home appliances; IoT applications are becoming ubiquitous. 3
Machines and devices have been intelligentized and networked because of the emergence of the IoT; relevant devices and systems have used networks more frequently in various fields and environments. Therefore, hackers have begun to target IoT devices. In the past, hackers targeted vulnerabilities in information systems and webpages, whereas current information security challenges mainly include mobile data theft, automobile system cracking, and medical equipment invasion. Therefore, information security and privacy protection are crucial topics for the IoT.4,5
Radio-frequency identification (RFID) is a widely used technology in the IoT area. Tags of RFID store standardized and interoperable messages that are collected by RFID readers and transmitted to backend systems through wireless networks for processing. In this vision, the IoT forms a vast and interconnected knowledge network and achieves the intelligent management of objects.
Related protection/authentication mechanisms have been continuously developed. Weis et al.
6
first developed the concept of RFID reader authentication, whereby only authenticated readers could notify tags to enter their locked/unlocked state. Ohkubo et al.
7
subsequently proposed a one-way authentication protocol based on a hash chain. Dimitriou
8
devised a method ensuring mutual authentication (MA) between the backend database and tags, thus helping reduce the database load. Burmester et al.
9
developed an authentication mechanism known as O-TRAP, in which the server and tags stored a random number
The aforementioned research results remained the problems with IoT devices that lie in unsecure communication and inadequate identity verification, which may easily result in user data leakage.19,20 According to the Global Risks Report published by the World Economic Forum in 2015, IoT risks have contributed to security challenges such as large-scale cyber-attacks, massive data forgery and theft, and the suspension of key information infrastructure and networks. From the aforementioned points, it can be seen that IoT-related devices and Internet infrastructure are expected to face severe information security problems, which will result in major losses.
In this study, we proposed a matrix-based RFID authentication approach for IoT applications. The proposed approaches can not only provide privacy with regard to location, but also fulfill the requests of confidentiality, unforgeability, and scalability. Moreover, this mechanism can improve server performance when processing a large amount of RFID data and effectively protect against denial-of-service (DoS) attacks.
The proposed protocol
In extending the O-TRAP protocol, this study developed a matrix-based authentication protocol that provides confidentiality and anti-counterfeiting, and protects users’ location privacy. The matrix’s low-level computation also enhances the server’s mass data processing capacity, thereby achieving system extensibility. The mechanism of this protocol is described in the following paragraphs.
The reader, the backend server, and the RFID tag are the three main hardware components of the proposed protocol. During communication, the server and the reader’s channel is secure, while the reader and the tag’s channel is not. The following notations are defined clearly in Table 1.
Parameter definition.

Setup phase
In the primary setup, the server can select three secret square

The proposed protocol.
Execution phase
The proposed protocol includes the following steps. Especially, the random values used here will be generated by cryptographically secure pseudorandom number generator (CSPRNG). A PRNG proper for security applications is known as a CSPRNG. A need for a CSPRNG is that an adversary not realizing the seed has only negligible advantage in distinguishing the generator’s output sequence from a random sequence. In other words, as a PRNG is only required to pass some statistical experiments, a CSPRNG must succeed in all statistical experiments that are restricted to polynomial time in the size of the seed. In C# program, the class RNGCryptoServiceProvider of cryptographic service provider (CSP) implements the concept.

If equation (1) is true, then the server believes that the received message has been sent by a valid tag. Otherwise, the server informs the reader to restart the communication or reject this communication.

In the proposed protocol, the server uses a pair of keys
Security analysis and comparison
We illustrate our proposed protocol that can achieve the aforementioned requests. In addition, we compare the performance of the proposed protocol with other related protocols.14,15,18,21–24 We make

Location privacy
We assume an argumentation through the Location-Privacy game in order to ensure that the proposed protocol offers location privacy. The following Location-Privacy game is conducted between a challenger
Location-Privacy game
Initial phase
The challenger
Query phase
Challenge phase
Theorem 1

Proof
The security of the proposed scheme can be formally determined as a game played between a challenger and an adversary
In this sequence game, we require the difference lemma to help our transformation of the games. In the following, we describe the lemma.
Lemma 1: difference lemma
We make

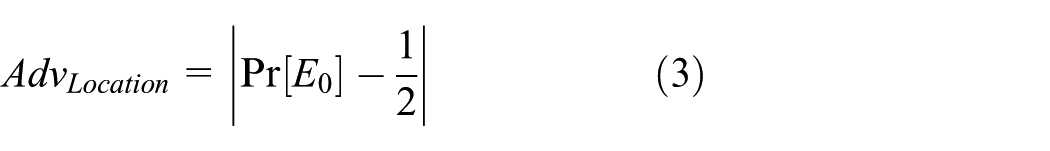

Obviously, the games



Obviously, if we make any queries, when

Combining equations (3)–(8), we obtain

Confidentiality
In the proposed protocol, the
Theorem 2
Confidentiality exists in the proposed protocol. Namely, all the private information, such as the
Proof
We make
Unforgeability
In order to offer unforgeability, the proposed protocol must provide MA. This subsection determines the security of MA and also presents it through the following MA model.
MA security
The MA of the proposed protocol is derived from the challenge–response method. An adversary
The MA model
Protocol participants
The tag and the server are the two participants of the proposed protocols. The tag and the server have to authenticate each other. Oracle is one thing that a participant may have many cases in the distinct concurrent executions of the proposed protocol. The notation
Long-term keys
The long-term secret key pair (
Oracle query
Within time
Hash(
Theorem 3
We make

where
Proof
By Theorem 2, advantage
When
When

Moreover,

Scalability
In the proposed protocol, the server exclusively implements one matrix multiplication,
In addition, when an attacker submits meaningless messages, the server can promptly authenticate them without matching other data again. This protocol can thus help resist DoS attacks.
Comparison
This subsection compares the proposed protocol with related protocols in terms of the aforementioned security requirements in Table 2. Chien and Huang 21 presented a lightweight authentication protocol which can achieve confidentiality and unforgeability, and resist DoS attacks, but the provided tag can be traced so that it cannot satisfy the requirement of location privacy. The same problem appears in the schemes of Huang et al., 23 Xie et al., 15 and Huang and Jiang. 24 Zuo 22 proposed the mechanism using XOR operation and one-way hash function to reduce mechanism loading, but it caused the desynchronization and impersonation problem. Although Dass and Om’s 14 mechanism achieves three requirements of security, because the number of transmitted messages between the tag and the reader (tag overhead) is high, the cost is higher in practice. In addition, Chen et al.’s 18 scheme also fulfills these requirements, but time cost is high (as shown in Table 3).
Comparison table with security requirements.

(1): confidentiality; (2): location privacy; (3): unforgeability; (4): complexity; (5): tag overhead.
Comparison table with computation costs.

R: computation cost of producing a random number; H: computation cost of a hash function; M: computation cost of matrix scalar multiplication; ROT: computation cost of rotation; CRC: computation cost of running a cyclic redundancy code; XOR: computation cost of XOR operation; SYM: computation cost of symmetric encryption or decryption; MOD: computation cost of modulo.
Table 3 shows the comparison of tag, reader, and backend database computation costs. Notably, the proposed protocol has the lowest reader computation cost because only the time to produce one random number is required. Regarding tag computation, because the cost of producing random numbers, performing XOR operations, and processing hash functions is extremely low, all the compared protocols require roughly the same time. Finally, the proposed protocol requires one matrix computation at most for the backend database (in this mechanism, as
Discussion
In recent years, the security of IoT devices has been debated; the security of a carefully designed IoT system can be compromised by unauthorized intrusion, but the security of a poorly designed IoT system may be compromised by poor design. How to balance the performance and security of embedded systems such as wireless network routers and network cameras will be a challenge for future end device developers. 26 According to the relevant information security literature, over the past 3 years, hackers have begun to shift their focus from web applications to IoT devices. Therefore, reinforcing the security of end devices has become an imperative topic to be addressed by developers in various areas: (1) Improper access control can enable unauthorized users to arbitrarily modify the relevant settings of an end device and even to control the entire device. (2) Lack of rigorous data protection mechanisms may enable hacks. Specifically, the absence of regulated encryption in transmission protocols or limitations in hardware specifications undermines the security of encryption. This enables hackers to easily extract and analyze the transmitted data in communication connections, thereby causing the problems of data leakage and tampering. (3) DoS attacks can use a small amount of abnormal data transfer to crash a system, resulting in failure in normal operations or services. (4) A device may involve insecure default password, a backdoor program, or a hidden account. Such an end device employs a relatively simple default password and does not provide users with any password-changing function. Backdoor programs or built-in hidden accounts may exist and enable illegitimate users to directly log in to the system as the system administrator to access and modify data or to control the end device.27,28
The 802.11x standard was the major wireless communication technology that previous network equipment adopted for wireless networks. However, alternative network communication technologies such as radio-frequency, near-field communication, and Bluetooth have begun to prevail in the IoT. However, these communication technologies can only transmit limited quantities of data over limited bandwidth at one time; they cannot provide a relatively safe and reliable communication mechanism. In addition, when most smart devices upload and save data to the cloud, the data pass through the connection layer, router layer, communication protocol layer, and the Internet layer before reaching the cloud, during which the data are transmitted through various devices and equipment; these diverse devices increase the risk of unauthorized data transfer. When an end device is transmitting unencrypted data through an unencrypted channel, if hackers steal the data, then the result appears as plain text. This may include the users’ account numbers, passwords, personal information, or other sensitive information. In addition, apart from the risk of unencrypted data leakage, the connection process may also be hijacked by hackers. Hackers may tamper with or counterfeit packet data to bypass security check mechanism, avoid identity authentication to achieve unauthorized access, or modify the configuration files in a device or backend system. 29
Of the various components of the IoT, backend systems play an essential role, and such systems are mostly implemented on the cloud. A typical end device passes time-consuming operations to a backend host for execution. For example, end devices can send their data back to the cloud host system directly or through a home gateway, after which the backend system can perform processing based on the data. At this point, the security of the cloud host plays an extremely crucial role: if the host is compromised by a hacker, it not only causes leakage of data on the cloud, but may even grant the hacker control over the user’s device through the interconnected features of the cloud and the device. Operating systems and application suites must be inspected regularly to ensure that hackers cannot exploit known vulnerabilities in outdated software to invade the system. Apart from the security of the applications or operating systems in the host system, attention should also be paid to the use of correct parameters and secure protection on cloud servers to ensure the security of the backend system. 3
Mobile devices are now commonly used in personal life, and almost everyone possesses a smartphone. In the future, mobile devices such as smart bracelets or smart glasses will be more closely linked with users. They will also be closely connected to the IoT. Numerous end devices or backend systems will enable users to access data through mobile applications; thus, security measures for mobile devices and mobile applications are as essential as those for ordinary end devices or backend systems. The common security problems in mobile devices are and will continue to be similar to the aforementioned problems of end devices, including improper authority management, lack of encryption protection, bypassing of authentication and authorization, and logic loopholes. Hackers can determine a mobile device’s security vulnerabilities by analyzing its applications, can steal users’ accounts and passwords or relevant personal data, and can control end devices through mobile device applications. 30
As mentioned previously on IoT-related security issues, it can be found that a mechanism of low-level computation, protection of information privacy, prevention of fake identity, as well as maintenance of system functioning is needed, in particular the RFID-based system to be widely and generally used.
Constrained by inherent restrictions, 31 however, RFID tags have two major drawbacks: first, when the reader issues a query, the RFID tag automatically responds to the reader without notifying the owner; second, due to cost constraints, RFID tags are not able to perform thorough encryption and decryption operations to prevent the private information from spreading. Because RFID tags and readers communicate through transmission,6,7 it is noted that the two drawbacks lead to three major safety hazards: personal information and privacy exposure, malicious tracking, and counterfeiting behaviors.
In order to resolve the abovementioned security issues (personal information and privacy exposure, vicious tracking, and counterfeiting), this study suggested that a communication protocol for RFID systems should possess the following features:
Numerous protocols and mechanisms have been introduced to provide the necessary requirements for improving RFID communication security.9–18,25,32–36 However, cost- and security-related problems, such as additional hardware expenses, disclosure of users’ location privacy, or increasing server load, still exist and cannot be simultaneously resolved using only one mechanism. This study thus developed a security authentication mechanism that indeed achieves the following four advantages:
To be functionally carried out by a large amount of RFID data;
To satisfy confidentiality, anti-counterfeiting, and privacy protection;
To effectively protect against DoS attacks.
To be applicable to various conditions with the IoT RFID system (medical, logistics, transportation, access security, and so on).
Conclusion
In this study, we proposed a matrix-based RFID authentication approach for IoT applications. Not only can the proposed approach provide privacy with regard to location, but also fulfill the requests of confidentiality, unforgeability, and scalability. Specifically, we prevent some typical problems of RFID systems, that is, revealing users’ tracks and causing server overhead issues. Analyses and proofs prove that the proposed scheme is secure, suitable, and efficient for implementation in various IoT environments. This authentication mechanism will be accomplished and validated soon.
