Abstract
Introduction
Currently, cyber-physical system1–7 that has a wide range of application in industries such as factory, farm, veterinary, transportation, aviation, health care, and chemistry plays an important role in constructing an interaction system between cyber and physical elements. However, several security aspects should be carefully examined to successfully combine cyber-physical systems with various technologies. Current networks of energy grids, water supply, logistics, transportation, and so on comprise structures that are vulnerable to external malicious attacks. Data in the industrial cyber-physical system are usually critical, and they must be protected.
The cyber-physical system is based on an embedded system; therefore, it is necessary to consider the limited system resources in such a system. In addition, the encryption and decryption times are crucial because a low delay in control and response is required in cyber-physical system. In other words, the functions of the cyber-physical system should be designed based on algorithms with low computational complexity and high efficiency of resources. Generally, when the key length of the asymmetric key system increases, the encryption efficiency decreases due to the increased CPU time or memory requirements while implementing a cryptographic system. The amount of data to be sent and received also increases, thereby requiring more bandwidth for communication.8–10 Therefore, existing cryptosystems such as Rivest–Shamir–Adleman (RSA) 11 or homomorphic encryption 12 are difficult to deploy in the cyber-physical system environment due to the large key size of the encrypted data.
Elliptic curve cryptosystem13–16 is a cryptographic system that uses the computational complexity of the discrete logarithm problem on elliptic curves. It is an asymmetric key-based cryptosystem that has gained popularity in recent years due to the advantage of having a similar degree of safety with shorter key lengths compared to the conventional asymmetric key-based cryptosystem. Especially, security of the elliptic curve cryptosystem increases almost exponentially with the increase in the key length, and it has a considerable advantage in terms of rate of increase in the key length. This is a result of long-term technological advances compared to the existing asymmetric key cryptographic system with a quasi-index function. For example, the RSA cryptosystem must use approximately 15,000 bits of composite number to provide security similar to the elliptic curve cryptosystem of approximately 512 bits. 11
This study proposes the m-folding method–based elliptic curve cryptosystem for the industrial cyber-physical system. M-folding improves the scalar multiplication operation in elliptic curve cryptosystem by representing the number of multiplication count of a point as a bit string and further dividing it into arbitrary length. The elliptic curve cryptosystem architecture based on the m-folding method for the industrial cyber-physical system is also proposed in this study. Performance evaluation shows that the proposed method shows 50% faster encryption than the existing methods.
The rest of the article is organized as follows. Section “Related work” describes the related work and section “M-folding method-based elliptic curve encryption technique” describes the elliptic curve–based cryptosystem suitable for the industrial cyber-physical system. The performance evaluation results of the proposed method are presented in section “Performance evaluation.” Finally, section “Conclusion and future work” presents our conclusion and suggests future work.
Related work
Cyber-physical system
The cyber-physical systems1–7 are the next-generation network-based distributed control systems that combine physical systems having sensors and actuators with computing elements that control them. The advances in the cyber-physical system technology are a key factor in making life more convenient and efficient; however, the risk and vulnerability in terms of safety have increased. Cyber terrorism is no longer limited to information security in virtual spaces such as computers or Internet servers but is capable of attacking the actual control system, which is a critical issue that could directly threaten our lives and shake the foundations of nations. An example of the first attack on control systems is the Stuxnet virus 17 discovered in Iran in 2010. Cyber-attacks on various daily life or critical infrastructure have been reported since then. Therefore, the study of safety and security of cyber-physical systems has become more urgent and important than anything else.
A low delay in control and sensing is necessary in the cyber-physical system; therefore, the encryption and decryption times are crucial in such systems. The functions of the cyber-physical system should be designed based on algorithms with low computational complexity and memory usage. Symmetric key algorithms must use the same encryption key between the receiver and the sender and deliver the encryption key. It is not applicable for the cyber-physical system because a large number of devices need to communicate in order to share the same encryption/decryption key. Public key systems such as RSA and elliptic curve cryptosystem were designed to overcome the aforementioned limitations. The elliptic curve cryptosystem is more suitable in the cyber-physical system scenario due to its smaller key size. When the key length of the public key system increases, the number of computations and memory usage also increases with the increased size of the encryption data. Therefore, existing cryptosystems such as RSA 11 and homomorphic encryption 12 are difficult to deploy in the cyber-physical system environment.
Elliptic curve cryptography is gaining popularity in the field of cyber-physical system security due to its public key scheme and smaller key size compared to existing asymmetric key-based cryptosystem. Elliptic curve cryptography has several applications in the cyber-physical systems such as medical cyber-physical system encryption, 18 wireless sensor network infrastructure, 19 and key agreement in the smart grid. 20 However, none of these applications considered improving the encryption and decryption scheme for elliptic curve cryptography deployed in the cyber-physical system environment.
Elliptic curve cryptography
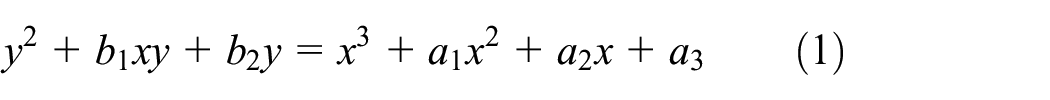
Elliptic curve cryptography8,9 is a cubic equation with two variables. The general elliptic curve equation is given by equation (1)
Elliptic curve in real number space uses an elliptical curve in a special category such as equation (2)

In an elliptic curve encryption technique, if

Three cases of elliptic curve.
In case of

In case of

In the case when
Fast scalar multiplications for elliptic curve cryptography
The main computation performed by the elliptic curve–based encryption technique is the computation:
Binary method
The binary method23,24 is a technique of expressing d in binary numbers by reading from the most significant bits sequentially and processing according to the following conditions:
If the bit is 0, perform point doubling.
If the bit is 1, perform point addition with
The binary method represented by a specific algorithm is shown in Figure 2. For example, as shown in Figure 3, to calculate 186P, 186 is expressed as binary number 10111010 and processed according to the algorithm in Figure 2. However, simply adding

Algorithm of binary method.

Computation process of binary method.
M-ary method
The m-ary method
25
is a computation technique for reducing the number of digits by generalizing what is expressed as binary number in the binary method. The format of expression used by this method is
The m-ary method represented by a specific algorithm is shown in Figure 4. For example, to calculate 186P, 186 is expressed as tetramal 2322 and processed according to Figure 5. Storing even numbers such as 2P, 4P, and 6P in the m-ary method can waste memory. For example, 2P is two times P, 4P is four times P, and 6P is two times 3P. As shown by the algorithm in Figure 4, point doubling is performed on each loop basically and with only P or 3P. 2P, 4P, and 6P can be calculated with the same number of calculations. Therefore, information from 2P, 4P, and 6P being unnecessary information can waste memory.

Algorithm of m-ary method.

Computation process of m-ary method.
Window method
In the window method,
26
when

Algorithm of window method.

Computation process of window method.
The window method stores only odd multiples such as P, 3P, and 5P; therefore, it does not encounter the memory space problem of the m-ary method. Consequently, it is possible to store a higher multiple of P values using the same memory space when compared to the m-ary method. However, the memory may be wasted in other ways, for example, if the window size is three, the look-up table stores 3P, 5P, and 7P; however, there may actually exist values referenced less than two times. In addition, as shown in Figure 7, the value 7P is not used, which can result in memory wastage.
Scalar-folding method
In the scalar-folding method,
27

Algorithm of scalar-folding method.
Analysis of existing methods
The existing methods solely focus on decreasing the number of computations in a general scenario. In the cyber-physical system environment, where a large number of devices are deployed and authentication keys do not change frequently with p, a scheme that can take advantage of pre-computed look-up table can greatly improve the real-time encryption/decryption performance of the elliptic curve–based cryptosystem. We propose the computation method that can flexibly fold a bit string in arbitrary size and utilize a pre-computed look-up table.
M-folding method–based elliptic curve encryption technique
M-folding method
This study proposes the m-folding method. It divides a bit string into

Algorithm of proposed method.

Computation process of proposed method.
Elliptic curve–based cryptosystem architecture
This study designed the m-folding method–based elliptic curve cryptosystem architecture for the industrial cyber-physical system. Figure 11 shows the proposed architecture. M-folding method–based elliptic curve cryptosystem comprises an encryption management module that performs encryption and decryption, an elliptic curve management module that executes an m-folding method–based elliptic curve encryption algorithm, and a key management module that manages the encryption keys.

Elliptic curve–based cryptosystem architecture.
Encryption management
This module encrypts the messages generated by the message generator in the message module through the encryption process or receives the encrypted messages from the network and sends the messages decrypted by the decryption process to the message parser in the message module. The encryption and decryption algorithm simulates the ElGamal cryptosystem among asymmetric key-based encryption techniques. The encryption and decryption processes are given by equations (5) and (6). First, a point


The decoding calculates

Stability of the elliptic curve
28
is based on the computational complexity of solving the elliptic curve logarithm problem. For example, if an intruder has obtained
Elliptic curve management
This study uses the elliptic curve equation recommended by the Korean certificate–based digital signature algorithm using elliptic curve (EC_KCDSA). 4 The equation generator generates and manages finite field variables that are necessary to define the elliptic curve equation. EC-KCDSA recommends two types of elliptic curves to be used for encryption: arbitrary curve given by equation (8) and the Koblitz curve given by equation (9)
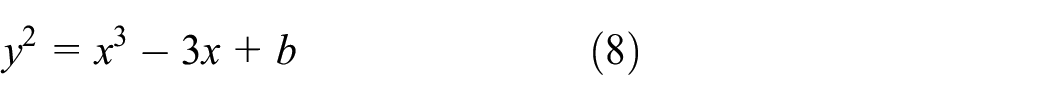
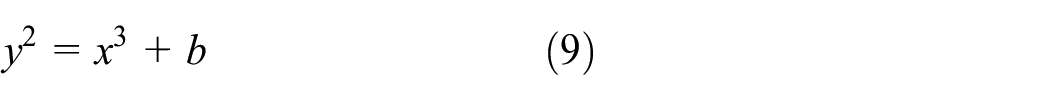
The elliptic curve equation in this study is based on the Koblitz elliptic curve equation because it can be calculated efficiently and can consequently ensure faster encryption. The elliptic curve arithmetic module defines the operations required for the encryption module, for example, finding points on an elliptic curve or addition operation between two points.
Key management
The private/public key generator generates public and private keys for encryption and decryption based on elliptic curve. The public key selects an arbitrary point
Performance evaluation
During performance evaluation, performance of the m-folding method was compared with existing scalar multiplication algorithms in the following three conditions: (1) when look-up tables are not used, (2) when look-up tables are used, and (3) when pre-computed look-up tables are used. When the look-up table is calculated in advance, it is not created each time the algorithm is executed; however, the created table is stored at a known location and reused. The performance evaluation compares the processing speed of
Case when look-up table is not used
Figure 12 shows the performance result without the look-up table. Each algorithm showed a processing speed between 138 and 141 ms, thereby showing no significant difference in performance.

Case when look-up table is not used.
Case when look-up table is used
Figure 13 shows the performance when the look-up table is used. The window technique showed better performance when the look-up table had larger memory. As the size of the look-up table increases, the performance of m-ary method increases. However, after a certain level, the performance decreases because when a binary number is converted to the given base, the larger the value of

Case when look-up table is used.
Case when look-up table is created in advance and recycled
The performance results in Figure 14 show that when the look-up table is pre-computed, the processing speed increases when the additional storage size increases because the time to re-create the tables is saved. Compared to the window method, the m-ary method showed slightly better performance. M-folding method showed better performance than other algorithms when the storage space was two or more, and the processing speed was approximately two times faster when the storage space was four or more. On the contrary, the rate of improvement of the processing speed relative to storage size gradually decreased because the bit string of

Case when look-up table is pre-computed and recycled.
As a result, the proposed m-folding method shows good performance while using a pre-stored look-up table. Using pre-stored look-up table is suitable in an environment where the value of
Conclusion and future work
This study analyzed the elliptic curve algorithm that is more efficient than the asymmetric-based encryption technique and designed the encryption technique with improved performance by applying the m-folding method that is more efficient than the existing scalar multiplication algorithm. This technique can mitigate the resource constraint problem; therefore, we used it to design the m-folding method–based elliptic curve cryptosystem structure suitable for the industrial cyber-physical system. However, the performance evaluation results showed excellent performance only when the look-up table is pre-computed and recycled.
In the future, it is necessary to research a cryptosystem that can improve the security of the industrial cyber-physical system using an encryption technique with high security and efficiency such as elliptic curve algorithm or comprehensively researching a high-performance technique regardless of a look-up table.
