Abstract
Keywords
Introduction
As the core technology of Industry 4.0, cyber-physical system (CPS) is becoming a global technology industry to support and lead a new round of technological evolution, and have a significant impact on economics and social lives. Up to now, CPS has been widely used in many domains; typical application scenarios include manufacturing, transportation, healthcare, urban construction, and so on.
CPS requires tight integration and cooperation of computing, communication, and control technologies 1 (Figure 1). Due to such integration, CPS has greatly improved system efficiency; meanwhile make the system more vulnerable to attacks. 2 In addition to traditional cyber-attacks, CPS also suffers from attacks that break down physical plants (such as sensors and actuators), owing to the various physical plants involve in CPS (Figure 2). Break down of these plants usually result in great damages, for example, the Stuxnet worm attack incident happened in 2010 that targeting the centrifuges of Iran’s Bushehr nuclear power plant, and the Maroochy-Shire water breach happened in 2000 that targeting sewage pumping stations. Against such attacks, traditional information security techniques 3 (such as access control, data encryption, network isolation, authentication, and so on) seem insufficient, as they do not make full use of the knowledge about whether the measurements are compatible with the corresponding physical process or control mechanism, and they cannot deal with insider attacks and attacks targeting the physical dynamics. 4

Cyber-physical system.

Attacks that break down physical nodes.
Summary of related work
For the above reasons, the research of CPS secure state estimation and attack reconstruction from the perspective of control theory has received plenty of attentions in last several years. 5 For instance, in Fawzi et al., 6 secure state estimation and control for continuous-time CPS under adversarial attacks is investigated, while attack reconstruction is not considered, and it assumes that the set of attacked nodes is fixed. In Chang et al., 7 Kalman filter is used for CPS secure estimation, and the limitation about fixed attacked nodes is released. In Lu and Yang, 8 switched Luenberger observer is adopted for secure state estimation with CPS case, but only disturbance and sensor attack are considered, and does not take attack reconstruction into account. There are also some bibliographies focus on attack reconstruction. In Song et al., 9 two adaptive sliding mode observers with on line parameter estimation are designed to solve the problem of attack detection and reconstruction, though the estimation of sensor attack and actuator attack are executed separately, and external disturbance has not been considered. In Corradini and Cristofaro, 10 state and sensor attack observer is designed using sliding mode, and external disturbance is taken into account in order to achieve robust estimation performance, while discrete-time CPS case is not considered. In Shi et al., 11 a stochastic modeling framework is introduced for joint state and attack estimation in CPS; nevertheless, actuator attack is absent, and discrete-time CPS case is not considered yet. In Wan et al., 12 distributed observers are designed to reconstruct the node states of multi-agent system with Lipschitz-type nonlinear dynamics, and the reconstructed states are used for feedback control, but only sufficient conditions are derived, and the discrete-time case is not considered. There are also some other results and developments in this domain, see in Hu et al., 13 Corradini and Cristofaro, 14 Lu and Yang, 15 Xie and Yang, 16 and the references therein.
Main contributions
In this article, we focus on how to estimate secure state and reconstruct actuator attack simultaneously for continuous-time/discrete-time CPS. While most existing results only consider continuous-time CPS case, and there are few results about discrete-time case. To achieve the aforementioned goal, an intermediate and robust observer is proposed. The main contributions of this article are as follows. (1) A new observer is designed, based on which the reconstruction of secure state and actuator attack are executed simultaneously with
Organization
The rest of this article is organized as follows. In section “Methodology,” a common CPS model is described with continuous-time/discrete-time form, and some reasonable assumptions are stated. Next, an intermediate and robust observer is designed, then an augmented form is deduced, based on which two theorems and their corollaries are presented to obtain the observer gain matrices. The illustrated examples are presented in section “Results and discussion” to prove the availability of our proposed scheme, and conclusion is given in section “Conclusion.”
Notation
For a matrix
Methodology
Preliminaries and problem formulation
Consider the following common form of continuous-time/discrete-time CPS model


where operator
Remark 1
The CPS model (equations (1) and (2)) describes a general system that suffers from actuator attack and external disturbance, which is very common in actual scenarios. Our goal is to estimate the happened attack and system state simultaneously for continuous-time/discrete-time CPS, which is a challenging work and has not been completely solved yet in the past literature. Future study will focus on joint reconstruction of actuator attack and sensor attack, and security control for CPS under attacks, on the basis of reconstruction approach proposed in this article.
Some assumptions are put forward as follows.
Assumption 1
For every complex number

Assumption 2
The external disturbance
Assumption 3
The actuator attack
Remark 2
Assumption 1 signifies the invariant zeros of the system
Remark 3
Assumption 3 only requires the first derivative of actuator attack to be norm bounded, while the attack itself could be unbounded, this is more general than the previous approaches presented in Song et al. 9 and Corradini and Cristofaro.10,14
Observer design
Here, an intermediate variable17,18 is defined as

where

for discrete-time case, we yield

where
Then, based on equations (1)–(5), the following observer is constructed as

for continuous-time case, the differential equation of the observed intermediate variable is

for discrete-time case, the difference equation of the observed intermediate variable is

for both continuous-time and discrete-time cases, the output equation under observer condition is

the actuator attack reconstruction equation under observer condition is

where
According to equations (6)–(10), it is obvious that the design of intermediate and robust observer is summed up to seek out adequate
Denote the error variables

Then, the error dynamics for continuous-time case are given by

and for discrete-time case, the error dynamics are given by

After analyzing the above error dynamics, the following augmented system is obtained in order to calculate gain matrices

and for discrete-time case

Let
Then, equations (11a) and (11b) can be simplified as follows

Remark 4
From equation (12), we can see that
Remark 5
We can also find that the system dynamics is finally deduced as error dynamics form as shown in equation (12), then the existing result presented in Gahinet and Apkarian
19
may be used, which helps turning the
Gain matrices design
The following theorems give the solutions to obtain gain matrices
Theorem 1 (for continuous-time CPS)
Provided that Assumptions 1–3 hold,


Proof
By directly using Lemma 4.1 in Gahinet and Apkarian, 19 which is called Bounded Real Lemma, equation (13) is obtained.
For equation (12), let
Theorem 2 (for discrete-time CPS)
Provided that Assumptions 1–3 hold,


Proof
Similar to Theorem 1, the proof is omitted here.
Remark 6
The obtained conditions (equations (13)–(16)) are not strict linear matrix inequality (LMI) conditions due to the two different Lyapunov matrices
Corollary 1 (for continuous-time CPS)
Provided that Assumptions 1–3 hold,


then, error equation (12) for continuous-time case satisfies
Corollary 2 (for discrete-time CPS)
Provided that Assumptions 1–3 hold,


then, error equation (12) for discrete-time case satisfies
Remark 7
Based on Corollary 1 and Corollary 2, the minimization problem of
Minimize
Subject to equations (17) and (18) for continuous-time case;
Or equations (19) and (20) for discrete-time case.
Results and discussion
In this part, we consider an unmanned ground vehicle (UGV) system presented in Shoukry and Tabuada, 21 include continuous-time/discrete-time case, to prove the availability of our proposed scheme.
Example 1
Consider the continuous-time UGV model under actuator attack and external disturbance, which is described as follows

where
It is obvious that the above given UGV model is the form of equations (1) and (2). The external disturbance is set as 0, the actuator attack is created as in Table 1, which meet Assumption 2 and Assumption 3.
The actuator attacks

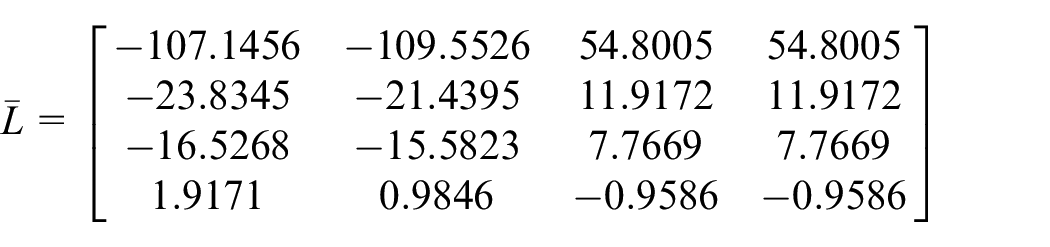
Solving the inequations in Corollary 1 with

The observer gain matrix is

For given

Actuator attack components and their estimated values.

Observation errors of actuator attack components.

System state components and their estimated values.

Observation errors of system state components.
From Figures 3 and 4, we can see that the observation value of actuator attack can track the real attack simultaneously, and its observation error has a peak at the moment of attack occur and converges quickly. Figures 5 and 6 show that the observation value of UGV position and linear velocity can also track the real state well. Meanwhile, due to the observation gain matrix is calculated offline, the possible performance penalty introduced by proposed solution is negligible. It can be illustrated that the proposed solution has achieved desired estimation performance under continuous-time CPS case.
Example 2
Consider discrete-time CPS model (equations (1) and (2)) with

which is the discretization of the aforementioned Example 1 using zero-order holder with a sampling period
Solving the inequations in Corollary 2 with
For given

Observation errors of actuator attack components.

Observation errors of system state components.
Conclusion
In this article, we study the problem of secure state estimation and actuator attack reconstruction simultaneously for continuous-time and discrete-time CPS. By introducing an intermediate variable, a novel intermediate observer is designed. By denoting the error variables about system state, intermediate variable, and actuator attack, an augmented error dynamics equation is obtained based on matrix augmentation technique. Then, a regional pole placement method and a Bounded Real Lemma are used to obtain robust and less conservatism results. The proposed scheme is verified effectively by the illustrative examples.
The present work only considered CPS that suffers from actuator attack and external disturbance, sensor attack is absent, so our future study will focus on secure state estimation and attack reconstruction that under both actuator attack and sensor attack.
