Abstract
Keywords
Introduction
Wireless device-to-device communication has been used in many recent applications such as mobile social networks. Wireless mobile communications (WMNs) are subjected to various security threats, which involve identity spoofing, eavesdropping, and man-in-middle attacks. 1 Due to seamless mobility, providing security to the mobile station (MS) is challenging in WMN.
Authentication is used to authorize an MS for secret communication. Each MS that is outside the range of its home network requires authentication in the visited network. 2 In the absence of powerful authentication techniques, a mobile network is said to be unprotected so that the message contents may be exposed or modified by a malicious attacker. 3
Recently, the Authenticated Key Agreement (AKA) protocol has been applied in many WMN applications such as multimedia mobile IP, since it ensures secure and reliable communications. The two types of AKA protocols are Authenticated Group Key Agreement protocol (AGKA) and two-party AKA (2PAKA) protocol. The AGKA protocols provide a common secret session key for two or more users, whereas the 2PAKA protocol establishes a common session key between the users. In both of the protocols, the users encrypt their messages using the session key, which is then exchanged between them.4,5 Apart from its advantages, the EPS-AKA protocol has many vulnerabilities. 6 To provide confidentiality to the transmitted messages, encryption is used. Though encryption protects the messages effectively, it is inefficient due to high computations particularly for mobile devices. 7
In User-to-User Mutual Authentication and Key Agreement (UUMAKA), 6 the relative computation cost of the bilinear pairing is significantly higher than that of elliptic curve scalar point multiplication. 4 Hence, a pairing-free AKA protocol is necessary, which uses both ECC and IBC for two-party communication.
In this paper, Pairing-Free Identity-Based Mutual Authentication and Key Agreement (PIMAKA) scheme for WMN is proposed.
Related works
Xi et al. 1 have designed an AKA protocol for mobile devices. It utilizes channel state information as the common secret between the honest devices. It ensures that any device beyond the range is not able to access the keys. It supports group key agreement and protects channel attacks.
Hafizul Islam and Biswas 4 have proposed a pairing-free ID-2PAKA protocol based on ECC. It establishes a common session key between two users. It solves the security issues of previous AKA protocols and thus suitable for efficient P2P communications.
Shrestha et al. 8 have proposed a secure protocol, which applies the features of Kerberos-based ticket authentication. It distributes tokens to the mobile users to access the roaming users of home and foreign networks. It, thus, provides mutual authentication and session key establishment.
Farhat et al. 9 have proposed private identification, authentication, and key agreement protocol for mobile network. It mixes identification and AKA protocol to enhance the AKA protocol of UMTS network. It reduces the interrelated cycles of UMTS AKA and provides user privacy.
Jiang et al. 10 have proposed a privacy-preserving authentication protocol based on homomorphic encryption. It achieves anonymity for the mobile users by randomly generating the authenticated identities. Thus, it prevents the user’s identities from other users and service providers.
Roychoudhury et al. 11 have designed Hierarchical Group-based Mutual Authentication and Key Agreement (HGMAKA) protocol for 5G networks. The MAC used in HGMAKA results in effective resource utilization and resists authentication failures. It is also applicable in heterogeneous network architectures.
Naqash et al. 12 have analyzed the Rapid Development Authentication Protocol. It provides mutual authentication between User Equipment (UE) and femtocell for improved security. It protects from various attacks such as Sybil attack, DoS, eavesdropping, false data injection, and packet sniffing.
Bhattacharjee and Pal 13 have developed a mutual authentication technique for circuit and packet switching networks. It authenticates the subscribers and the network by means of passwords, identifiers, and biometric features of the subscribers.
Alezabi et al. 14 have proposed an Efficient EPS-AKA (EEPS-AKA) protocol, which is based on Simple Password Exponential Key Exchange protocol. It uses a secret key with smaller sized messages thereby reducing the authentication delay and storage cost.
PIMAKA scheme for WMNs
Overview
In this paper, PIMAKA scheme for WMNs is proposed, which consists of the following phases:
Setup and Key generation
Mobility Management Entity (MME) authentication and Proxy Signature generation
Proxy Signature verification and User-to-User authentication
System model and components
The various components involved in the LTE cellular system are as follows:
Figure 1 shows the system model. It consists of two UEs connected to a MME, which in turn is connected to a HSS. In this model, HSS generates the system parameters and exchanged with MME. The UEs send their authentication request and get authentication reply from MME, which are illustrated in the next section.

System model.
PIMAKA scheme
Phase 1: setup and key generation
The setup phase of pairing-free ID-2PAKA 4 protocol is used.
In Key generation phase, the public and private key of UEA is computed by PKG as follows:
The PKG chooses

and
where
Then the private key of UEA is computed as

where
2. Similarly, public and private key of UEB is computed as follows:
The PKG chooses

and
where
Then the private key of UEB is computed as follows

where
3. For MME
The PKG chooses

and
where
Phase 2: MME authentication and Proxy Signature generation
At UEA
UEA computes the request ReqA and send it to MME as follows

where


2. At UEB
Similarly, UEB computes the request Re

where IDB = IMEIB


3. Proxy Signature generation at MME
When MME receives Re
For UEA, MME computes

where
MME then checks the following condition is true

If the above condition is true, then MME computes and sends Re

Similarly, for UEB, MME computes

where
MME then checks the following condition is true

If the above condition is true, then MME computes and sends Re

Phase 3: Proxy Signature verification and User-to-User authentication
Here MME acts as a proxy, and UEA and UEB as designated verifiers.
At UEA:
When UEA receives Re
UEA computes the shared session key

For UEB:
When UEB receives Re
UEB computes the shared session key

Figure 2 shows the basic operations involved in the proposed PIMAKA scheme.
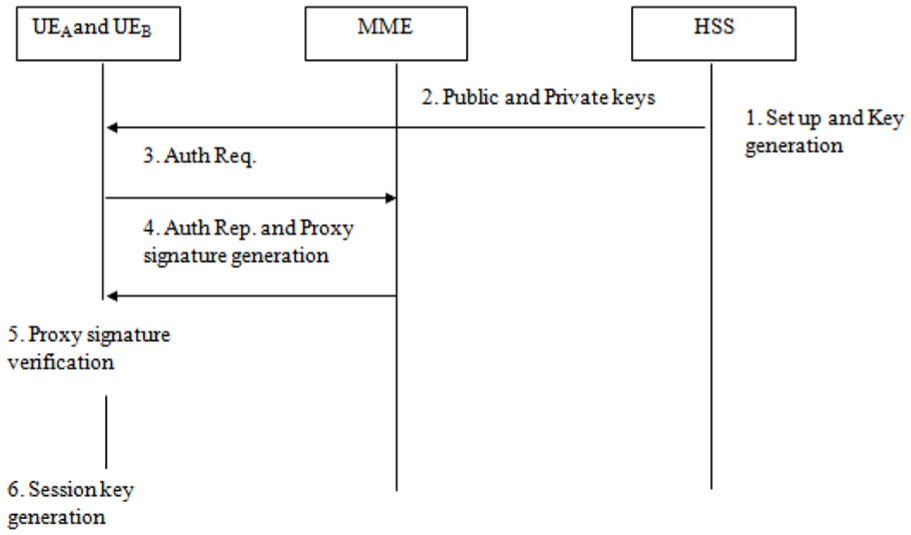
Basic operations of the PIMAKA scheme.
Simulation results
Simulation parameters
The proposed PIMAKA scheme is simulated using NS2 and compared with the UUMAKA scheme. 6 The simulation topology is shown in Figure 3. In Figure 3, there are 18 cells, each cell consisting of 6 wireless mobile users. The BS is deployed in the middle of each cell. The six service providers correspond to each row of the cell. The user 92 in cell 10 has been marked as an attacker.

Simulation topology.
The simulation parameters are given in Table 1.
Simulation parameters.

Performance metrics
Authentication delay
The total authentication delay (

where
Computational cost
To evaluate the bandwidth consumption of the reauthentication, all transaction message size between different network entity sections in one round of authentication session are calculated.
Authentication success ratio
Authentication success ratio (

where
Results and analysis
In the simulation experiment, the mutual authentication is performed between the users of different cells by varying the number of user cells from 3 to 18. The number of attacker per cell is kept as 1.
Figure 4 shows the authentication delay involved in both the schemes. As seen in the figure, the delay increases linearly for both the schemes. Since PIMAKA does not involve the computations of bilinear pairings, the authentication delay of PIMAKA is 41% less, when compared to UUMAKA.

Authentication delay for different cells.
Figure 5 shows the ASR measured for PIMAKA and UUMAKA schemes. As the number of cells is increased, the success ratios of both the schemes tend to decrease. But PIMAKA attains 16% higher success ratio when compared to UUMAKA.

Authentication success ratio for different cells.
Figures 6 and 7 show the computational and communication costs involved in PIMAKA and UUMAKA schemes, respectively. As depicted by the figure, the computational and communication cost of both the schemes increase when the number of cells is increased. Since PIMAKA does not involve the heavy computations of bilinear pairings, it has 72% lesser computational cost and 71% lesser communication cost, than the UUMAKA scheme.

Computational cost for different cells.
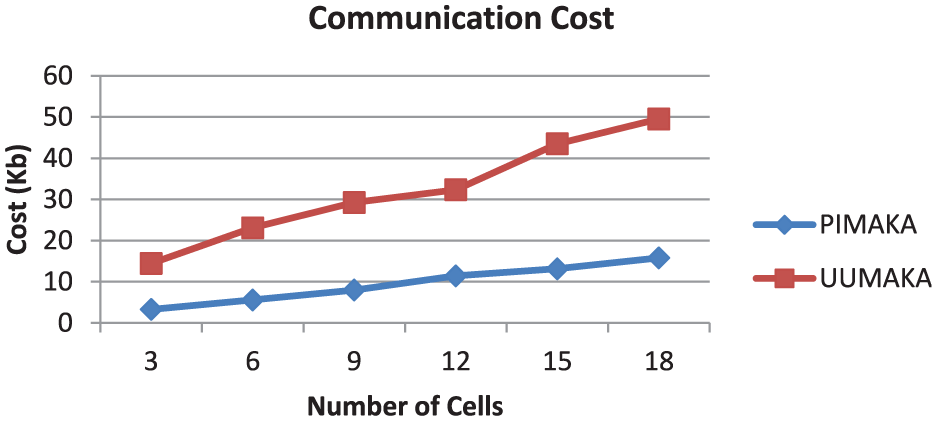
Communication cost for different cells.
Conclusion
In this paper, we propose a PIMAKA scheme for LTE networks. In consists of Setup and Key generation, MME authentication and Proxy Signature generation, and Proxy Signature verification and User-to-User authentication phases. Simulation results show that PIMAKA attains significantly less computational and communication cost when compared to UUMAKA scheme.
