Abstract
Keywords
Introduction
With the development of Internet of Things (IoT), the traditional industrial models have been gradually changed, triggering a new wave of industrial, economic, and social development.1–3 As a new form of Internet-based information technology, in addition to all the same types of cyber-attack threats as in the other wireless networks,4–6 the IoT field also faces more and more complex threats due to its multi-source heterogeneity, openness, ubiquity, and other characteristics. The issue of IoT security has also become one of the keys to development.3,7–9
Traditionally, solutions to the security of information transmission are provided through cryptographic protocols implemented at the upper layers.3,10,11 Yet, due to the characteristics of IoT, modern cryptographic methods alone may become insufficient for achieving the desired communication security in many practical scenarios. For example, low-end IoT devices are inconvenient to adopt highly complex cryptographic measures due to their limited energy and computational power. Although there are some lightweight encryption methods, the highly heterogeneous IoT systems without unified cryptographic protocols also make the management and distribution of keys very difficult. 12 As a result, it is imperative to explore complementary or alternative information security measures for IoT applications. Unlike cryptographic-technique-based security, physical layer security uses inherent properties of the channel uniqueness and reciprocity of physical channels that can achieve information-theoretic security regardless of eavesdroppers’ computational power. Physical layer security can provide an additional layer of protection without compromising the existing cryptographic-technique-based security protection, which has aroused extensive attention.13–15
In the related research of physical layer security, the cooperative jamming (CJ) is the mainstream technology, the core idea of which is to send artificial noise (AN) to confuse eavesdroppers.16,17 CJ-based methods have been used in various scenarios, for example, cognitive radio networks (CRNs)18,19 and heterogeneous networks.20,21 Li et al. 18 proposed a CJ scheme where secondary users (SUs) are selected as helpers to generate jamming signals to block eavesdroppers. Using the coalition formation game, they design an effective cooperation strategy to maximize secrecy capacity. Introducing the non-orthogonal multiple access (NOMA) technology into CRNs, Wei et al. 19 analyzed the security performance of SUs and derived a closed-form expression of the secrecy sum rate (SSR) of all SUs. Huo et al. 20 designed three different CJ schemes for different user requirements, with the cooperation of macro- and microcells. In scenarios where eavesdroppers’ channel state information (CSI) cannot be obtained, in some previous studies22–24 different physical layer security transmission schemes were designed, via secrecy encoding together with artificial-noise-aided signaling, pace power synthesis, and power allocation, respectively.
Naturally, this idea of CJ can be introduced into IoT networks to achieve secure transmission at the physical layer.12,25–27 Introducing the idea of cognitive radio into IoT to build a Consumer Internet of Things (CIoT) network, Li et al. 25 proposed a CJ scheme, in which a selected SU can harvest energy from a primary user (PU) and then use the harvested energy to send AN. Assuming that there is an error in the channel estimation, they optimized the worst-case secrecy rate in the presence of a single eavesdropper. Expanding the number of eavesdroppers from one to multiple, Hu et al. 26 derived the secrecy outage probability (SOP) assuming only the statistical channel state information of eavesdroppers (ECSI) can be obtained. Then they proposed a power allocation scheme to minimize the SOP. Zhang et al. 27 studied the role of relays in IoT and analyzed the security performance of a two-hop network. In their network, the nodes can be relays and jammers in two different phases.
No matter how extensive is the research on CJ, no one has studied the secrecy performance of CJ in the following scenarios: (1) all nodes are multi-antenna; (2) multiple eavesdroppers can cooperate to improve their eavesdropping ability; and (3) ECSI cannot be obtained. In fact, with the development of millimeter-wave and large-scale antenna array technologies, the evolution trend of IoT devices from single antenna to multiple antennas is irresistible. 28 With millions of devices, IoT networks can expose users to multiple eavesdroppers whose CSI may not be available due to their passive mode. Therefore, it is of great practical significance to study the CJ technology in multi-antenna scenarios with collusive eavesdroppers, which can promote the development of physical layer technology in the IoT field.
Motivated by the above issues, we designed a CJ scheme to fight collusive eavesdroppers without knowing ECSI in multi-antenna IoT networks. Specifically, we assume that all the considered nodes in our network are equipped with multiple antennas. Moreover, only perfect CSI for legitimate receivers can be obtained, while the ECSI of collusive eavesdroppers cannot. With the help of a friendly CJ node, the physical layer security transmission from a controller to an actuator is studied in this article. To the best of our knowledge, we are the first to study a CJ scheme in this more practical scenario. Our contributions can be summarized as follows:
We propose a CJ scheme that needs the cooperation of a controller (transmitter), an actuator (receiver), and a friendly jammer. Through joint optimization, the proposed CJ scheme can maximize the received signal-to-interference-plus-noise ratio (SINR) of the actuator while maintaining the jamming to the collusive eavesdroppers despite unknown ECSI.
We demonstrate the theoretical performance analysis of our proposed scheme through SOP analysis and asymptotic analysis. In the SOP analysis, based on computational mathematics, we derive two different closed-form expressions of the SOP: in the presence of cooperative nodes and in the absence of cooperative nodes. In the derivation process, we solve the problem of multiple integrals. In the asymptotic analysis, based on rigorous mathematics, we explore the impact of different system parameters on SOP.
In view of the fact that IoT devices are generally energy constrained, we propose a power allocation scheme to minimize the sum of transmission power while meeting the basic security requirements. We solve the power optimization problem which is non-convex and difficult to deal with.
The rest of our article is organized as follows. We provide our system model and formulate it in section “The system model.” In section “Secrecy analysis,” we present the theoretical performance analysis of our proposed secure transmission scheme through SOP and asymptotic analyses. Furthermore, we propose a power allocation problem and give the corresponding solution algorithm in section “The power allocation problem.” Finally, the numerical results of our schemes are provided in section “Numerical results” and our work is concluded in section “Conclusion.”
The notations used in this article are as follows. Bold upper and lower case letters denote matrices and vectors, respectively.
The system model
In this article, we consider the transmission of private information from a controller (Alice) to an actuator (Bob) in an IoT network, as shown in Figure 1. One or more passive eavesdroppers (Eves) may coexist on the network trying to eavesdrop on the private information. To prevent eavesdropping, Alice or Bob needs to select one of the surrounding neighbor nodes as a CJ source (called as Jammer). The selected Jammer broadcasts AN to confuse the eavesdroppers when Alice sends the private information to Bob. Note that the selection of Jammer is beyond the scope of this article.

A physical-layer-secure transmission model for IoT.
Alice, Bob, and Jammer are assumed to have
List of the main notations.

SOP: secrecy outage probability; CJ: cooperative jamming.
Received signals at Bob and S-Eve
Assuming that Alice transmits private information to Bob while Jammer broadcasts AN, the received signals at Bob and S-Eve can be formulated as


where
SINR
For enhancing the ability to decode the information, Bob and S-Eve can take different strategies to maximize their SINRs. Bob can work with Alice and Jammer, while S-Eve can use a more effective diversity receiving method. Next, we will describe their strategies.
Bob’s SINR maximization
Equipped with the multiple antennas, Bob can use the decoding vector


To maximize the received SINR of Bob, it is necessary to jointly optimize the precoding vector

Using singular value decomposition (SVD) and zero forcing beamforming (ZFBF), we can obtain the optimal solutions of the above problem, which can be given by Lemma 1.
Lemma 1
When



where
For the proof of Lemma 1, see Appendix 1.
As a result, we can derive the SINR at Bob as

where
S-Eve’s SINR maximization
In the worst case where eavesdroppers can conspire perfectly, the maximum ratio combining (MRC) is their optimal diversity receiving method to enhance their SINR. According to Sklar, 32 we can give the MRC weight as follows

After MRC, the output signals at S-Eve can be rewritten as

Therefore, the SINR at S-Eve can be further derived as


where
Secrecy analysis
In this section, we explore the safety performance of our proposed CJ scheme in terms of the SOP and asymptotic analyses. With or without a cooperative jammer, we derive the closed-form expressions of the SOP. Moreover, the asymptotic behavior of SOP is given by strict mathematical derivation.
SOP
Before signal transmission, assuming that the private information is encoded by Wyner’s 33 wiretap code, we can get the achievable secrecy rate of the transmission link between Alice and Bob as follows

where

are the achievable rates for Bob and S-Eve, respectively. Note that the rate
According to Wyner,
33
if

where
To derive the closed-form expression of SOP in equation (16), Proposition 1 is needed to be given first.
Proposition 1
The CCDF of

where
For the proof of Proposition 1, see Appendix 1.
According to equations (9) and (15), for a given value of

If we cannot find any node to be a Jammer, that is,
Proposition 2
Without Jammer, the closed-form expression of SOP can be characterized as

Proof
When

Similar to the proof of Proposition 1, the CCDF of

Accordingly, for a given

Hence, we have completed the proof of Proposition 2.
Asymptotic analysis
To better design a CJ scheme, it is meaningful to explore the influence of system parameters on
Property 1
When


Property 2
When


where
Property 3
When

For the proof of the three properties, refer to Appendix 1.
Remark 1
Property 1 demonstrates that, in the case of a sufficient number of S-Eve’s antennas, secure transmission is impossible despite the assistance of Jammer.
Remark 2
Property 2 implies that the continued increase in Alice’s transmission power is not always conducive to improved security.
Remark 3
Property 3 theoretically confirms that, if Jammer’s transmission power is sufficient, secure transmission can always be guaranteed.
The power allocation problem
Since IoT devices are generally energy constrained, the optimization of the power allocation problem in the design of IoT wireless networks is important, involving greenness and sustainability. Generally, the following two power optimization problems should be considered: (1) how to minimize the SOP given the limited global transmission power and (2) how to minimize the sum of the transmission power given the security requirements. In contrast, the latter optimization problem has more practical significance in real-time application scenarios, which is therefore mainly focused in this article. The purpose of this optimization problem is to save energy as much as possible while meeting the security requirements. In this section, we formulate this optimization problem and give the corresponding solution algorithm.
Formulation of power allocation
When considering the optimization of the transmission power of Alice and Jammer, not only must the security requirements be met, but Bob’s reliable communication requirement should also be met. In addition, each node has an upper limit of its transmission power. Thus, considering both the upper limit of the transmission power and the minimum quality of service (QoS) requirement of Bob, the power optimization problem





where
Optimization of power allocation
From the closed-form expression of SOP which leads to non-convexity, we can see that it is very difficult to directly solve this optimization problem. To deal with this problem, we use a relaxation method and Taylor expansion formula to convert it into a convex problem. Finally, an iterative algorithm is designed to get the solution of the original problem.
First, after some operations of transposition and equivalent substitution, we rewrite the constraints (equation (28b)) in the following form

where



According to the convex optimization theory, only when

Since the above formula is a linear function, after replacement, the constraint (equation (28b)) can be turned into a convex function (it is well known that convex functions minus linear functions are still convex functions). It is worth noting that
Eventually, the power optimization problem can be transformed into the convex optimization problem






Generally speaking, a convex optimization problem can be solved efficiently by common solvers such as CVX.
36
However, in order to obtain the solution of the original optimization problem

Remark 4
Algorithm 1 should be executed at the controller Alice due to its stronger computational power. To execute Algorithm 1, Alice needs to know the CSI between all the legitimate nodes. Alice can easily obtain the CSI between it and Bob by channel estimation, but it cannot obtain the CSI between Bob and the cooperative jammer. Therefore, Jammer or Bob needs to send the CSI to Alice before the execution of Algorithm 1.
Remark 5
Algorithm 1 is an algorithm based on the ideas of approximation and iteration. According to Yuille and Rangarajan, 37 after multiple iterations to solve an approximate optimization problem, the algorithm is proven to converge to the optimal solution of the original problem.
Numerical results
In this section, we provide the numerical results to verify the performance of our proposed schemes. Here, the power of AWGN is set to 1 mw (i.e. 0 dBm). Unless otherwise stated, other parameters are set as
Figure 2 illustrates the effect of the number of nodes’ antennas on the SOP with

SOP versus
As

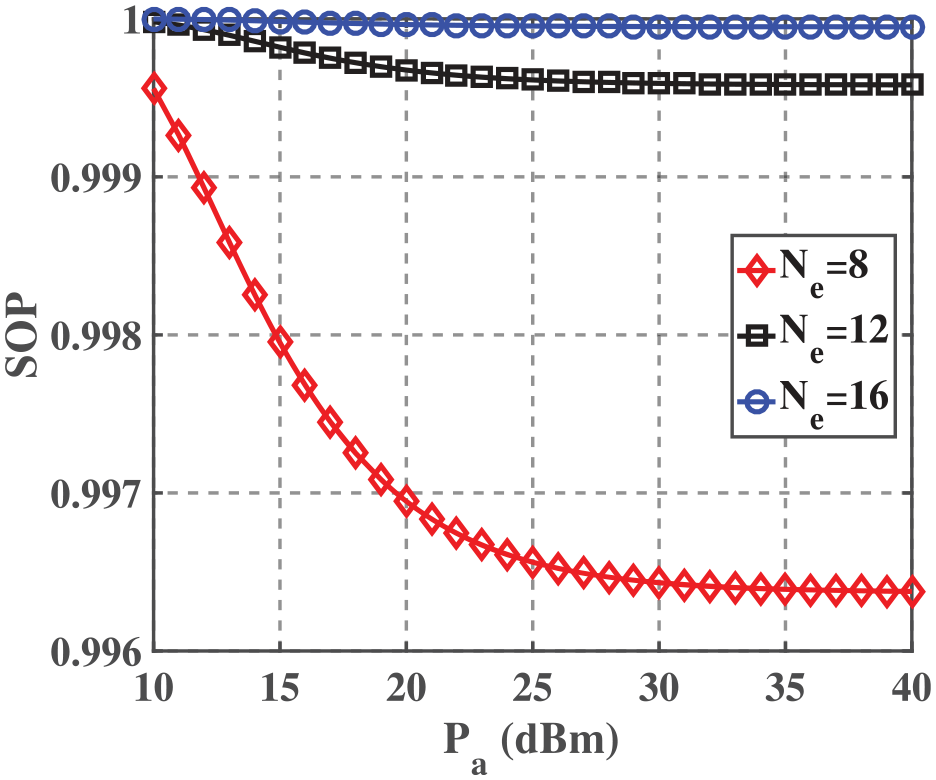
As we can see from Property 1 and Property 3, the effects of

In addition to SOP performance verification, we also perform Monte Carlo simulation experiments 10,000 times with random channel parameters to evaluate the impact of

ASR versus
In this article, we mainly focus on the power minimization problem, expecting to save energy in IoT devices. In Figure 7, we provide the convergence results of the proposed Algorithm 1 to solve this optimization problem. As we can see, the results are consistent with Remark 5 that the algorithm converges after several iterations. In addition to convergence, we can also draw the following conclusions from Figure 7: (1) the higher the requirements (including the security requirement and Bob’s reliable communication requirement), the higher the energy required, as shown in Figure 7(a); (2) the optimized

The convergence of Algorithm 1 for various variables with different requirements: (a) convergence of the objective function
Finally, we compare the performance of our proposed scheme with that of the methods proposed by Hu et al. 26 and Zhang et al. 27 as illustrated in Figure 8. To be fair, we set the transmission power of all transmitters to be 30 dBm in all the schemes, including source nodes, relays, and jammers. It is worth mentioning that only the transmitters are equipped with multiple antennas in Hu et al., 26 and all the nodes are equipped with a single antenna in Zhang et al. 27 According to the result in Figure 8, we can easily draw the conclusion that our proposed scheme with the advantages of multiple antennas is superior to the other two schemes in the fight against collusive eavesdroppers.

Comparison of performance.
Conclusion
In this article, considering multiple passive and collusive eavesdroppers in IoT networks, a CJ scheme is proposed. In the CJ scheme, by jointly optimizing the beamforming vector at a controller (transmitter), the decoding vector at an actuator (receiver), and the CJ vector at a friendly jammer (helper), the receiving SINR at the actuator can be maximized. Assuming that the eavesdroppers can collude perfectly, the closed-form SOPs with and without CJ are derived. Moreover, we provide some insights into the impact of various system parameters on the SOP by the asymptotic analysis. In addition, expecting to save the energy of IoT devices, we propose a power allocation algorithm to optimize the transmission power of devices, which can achieve the minimum total transmission power given the security requirements. Finally, the numerical results verify the theoretical analytical results and the effectiveness of the CJ scheme. Our scheme requires that CSI of legitimate nodes can be obtained perfectly. In view of the influence of channel estimation error, we need to further study secure transmission schemes under imperfect channels in our future work. And we just consider Rayleigh fading that is not comprehensive. Thus, in future work, we will also study the performance under other channel models.
